
It’s a classic case of the chicken and the egg:
How do I justify the cost of security tooling when I don’t have a security program?
How do I measure my security program if I don’t have security tooling?
The Organizational Security Maturity Model (OSMM) was exactly what I needed to communicate information security to my non-profit client. I could see the understanding on their faces as we talked through the model. We got “unstuck” and I was able to start focusing on other things…for a little bit, at least.
Knowing they didn’t have a lot to spend on tooling and that the technical teams were very pro-open source, I suggested some basic open source security tools to help monitor their environment.
“But why do we need those? Even if it doesn’t cost us money, it costs us time.” I stared at my client, confused. It was as if he had hired someone to renovate a building and was asking why the painters needed paint.
After riding high on the success of the OSMM, this was a sobering reminder that we’d only made one small step, not one giant leap.
There was no way to make the painter analogy without sounding like a jerk. “Let me pull together an ROI (Return on Investment) and we’ll go from there,” even though I had no idea what to do next. Realistically, an ROI wasn’t going to help here – the open source software wasn’t replacing human effort or an expensive platform, it was literally creating more (very necessary) work for the team.
Somehow, the Organizational Security Maturity Model needed to be translated to drive improvements in operations, even when they created a net spend rather than a net savings. I didn’t want to just slap a scale on it. But in looking at other maturity models, either from common frameworks or other consulting groups, that was the most obvious solution. If your scale is meaningful, it’s operational.
Since there were three major themes in the Organizational Maturity Model, the simplest thing to do was start with a three point scale. I distilled the Organizational Maturity Model to its three key stages.
With these three stages highlighted, the scale starts to take shape:
1. Little or no organizational understanding of information security.
2. Information security has an organization-wide structure, documentation and project management.
3. Security is considered a critical business and sales tool. Practices are repeatable, scalable and optimizable.

You can absolutely use the simple three point scale, but a five point scale gives more nuance. A five point scale defines the “between” states, allowing an organization to better see its progression. The difference between a 1 and a 2, or between a 2 and a 3, on a three point scale is a big leap for a smaller organization. The difference between a 1 and a 3, or a 3 and a 5, on a five point scale better delineates a path by defining the middle ground between them.
1. Little or no understanding of information security.
2. Information security efforts lack structure and organization. Even if processes are well defined, they are generally poorly documented. Successful efforts are localized and unlikely to be repeatable or scalable.
3. Information security has basic structure, documentation and project management; there is organization-wide oversight/insight even if scalability is an issue. Security likely be driven by compliance/regulation rather than an understanding of risk management.
4. Processes are well-defined, well-documented, repeatable and scalable, incorporating data analytics for insights. Information security is a risk management tool rather than a compliance tool.
5. Information Security has the program maturity and technology needed to provide near real-time insights to the executive team and business units. Focus is on process optimization for the entire organization, not just security.
Now that the scale was set, it was time to figure out how to use it!
What are we measuring?
In Technical Support Operations, I coached a lot of support engineers on how to troubleshoot and technical writers on creating troubleshooting guides. In troubleshooting a problem, whether it’s hardware or software, it’s helpful to break the system down into components. Problems can happen within a component, where two or more components interact, or at the interface to the user.
That’s why it’s helpful to think of an organization as a system, with security as one component. We need to understand what can go wrong with the pieces internal to security (i.e., the security component), the interactions of the security component with other business components, and how security is presented or interacts with the company’s customers.
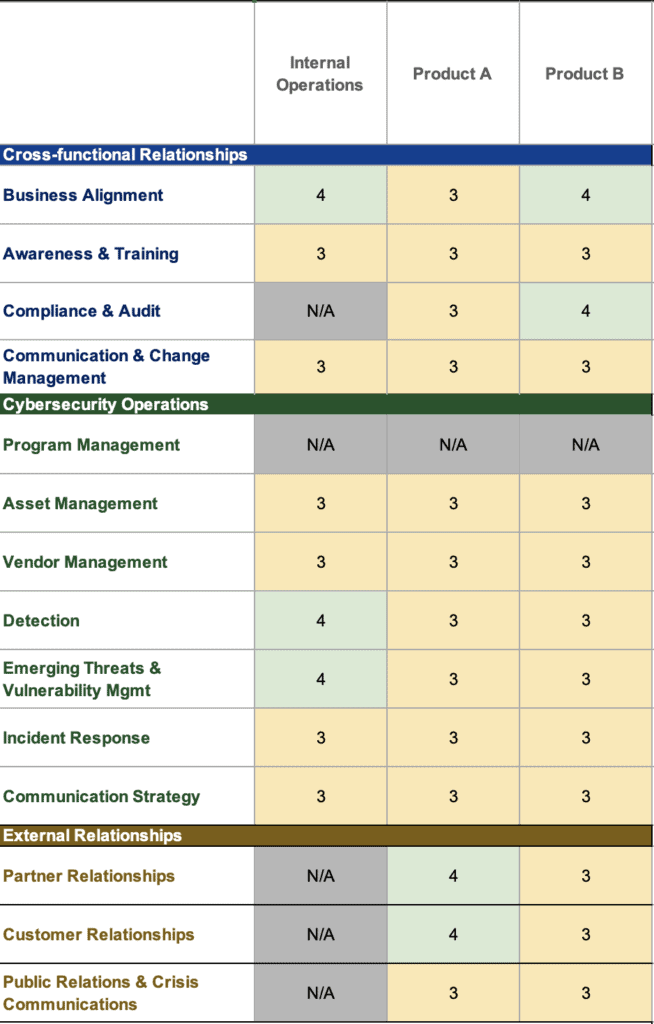
With this structure in mind, the maturity model measures the organization as a system, including its cross-functional relationships, cybersecurity operations, and external relationships.

Where are we measuring?
For larger or mature organizations, it’s often easiest to align these metrics to existing business units: Finance, IT, Marketing, Sales, Customer Service, etc. For smaller organizations or organizations without a traditionally defined structure, it can be as simple as Internal Operations and Product Lines.
An example of the Operational Security Model is below. This example company is measuring the security of its internal operations, along with two different products.

How are we measuring?
I like to start these as team discussions; this will often bring a balance between those who gloss over things and those that focus on the negative. Later, they’re easily updated as a part of your internal review or audit.
Use these questions to help you guide these discussions.

Now let’s assess one of these questions for the maturity model using our five point scale from above.
“Do employees know what to do or who to contact if they have security questions or concerns?” If the answer is…
- “How do I know if my question is related to security?” = 1
- “Yes, I pop into Slack and ping IT,” = 2
Follow up question = “What does IT do next?”- If IT has a process for handling this, great! They’re still at least a 2.
- If IT has an accurately documented process, even better! They’re now a 3.
- If IT has an accurately documented process AND that process can still function if your company suddenly doubled, this is best!! This is a 4!
It’s important to note that a “3” is the baseline – I tell new clients (who are usually all 1s or 1s & 2s when they come to us) that 3 is where I want them to be after six months. You’ll often find that someone, perhaps even an entire team, is behaving in a security conscious way. But if that process isn’t documented, that team is not achieving even the baseline of 3. All they have to do to reach the baseline is write down the existing process. That’s it! So while time consuming, it can be very easy for that team to reach a baseline of 3.
NOTE: I don’t expect any sub-500 person company to be a 4 or 5 – this requires a significant investment in security tooling that non-enterprise organizations usually can’t afford. If I can get a client to a 4 with good processes and some creative tooling, then great!
How often are we measuring?
My team at Fractional CISO creates an initial security maturity model as a part of the gap analysis with a new customer, then after six months together, so they can see their improvement. After that, yearly for very mature/stable organizations or biannually for growing organizations. The OpsSMM will help ensure that healthy security practices are maintained as an organization grows.
What does it look like?
Below, you’ll see that the organization we looked at in the model above has made some improvements after 6 months of work!
Where can I find the Operational Security Model?
The template for the Operational Security Model is in the same Excel file as the Organizational Security Model. Both can be downloaded for free from my GitHub and used under the Creative Commons license.
As always, I appreciate any constructive feedback! I’d love to know how folks are using this model and changing it to suit their needs.
Hopefully it helps to solve your organization’s own chicken-and-egg problem.
Want to get great cybersecurity content delivered to your inbox? Click here to sign up for our monthly newsletter, Tales from the Click.




