He just wanted a job.
Or so said a self-described penetration tester who compromised the hosting platform Packagist to replace abandoned PHP modules with ones he controlled. He didn’t deploy any malicious code, just a note that he was looking for a job. His compromise could have pushed malicious code to the over 500 million installs using the open source packages.
Open source code is everywhere in modern software. Even the largest projects frequently use old and neglected packages of open source code, which creates a frightening attack vector. A lot of software could be very vulnerable to this sort of attack, unless developers use a good security-first software development lifecycle (SDLC) to mitigate the risks.
Traditionally, software development focused primarily on functionality and meeting business requirements. However, as cyber threats continue to evolve, it has become clear that security should be an integral part of the SDLC.
Software Development Life Cycle (SDLC) Explained
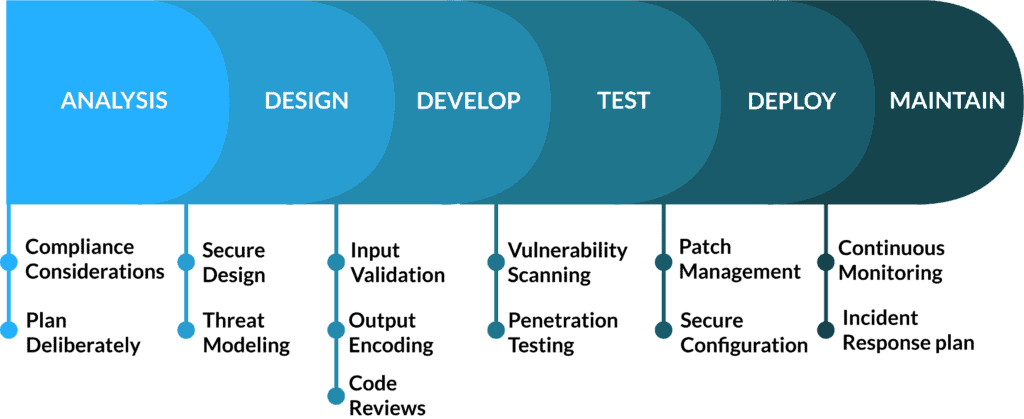
SDLC is a model used to break down and understand the different stages of software development. There are many different models for an SDLC, but for this article we will use a six-phase model.

SDLC, Quickly:
- Analysis is where the business need is identified and software is planned at a high level.
- Design is where the details of the program and how it will work are defined and laid out for the development team.
- Development is, as the name implies, the program is actually developed.
- Testing is where the mostly-completed program is tested for functionality, usability, and bugs.
- Deployment is the process of distributing the software to users.
- Maintenance is important to keep your users happy. Keep pushing updates and fixing bugs they discover until the end of the software’s lifespan.
What is this “S-SDLC” I keep hearing about?
S-SDLC stands for the Secure Software Development Lifecycle. This simply means that the SDLC is proposed and utilized with a security-first mindset. S-SDLC is a little confusing in that it doesn’t mean any specific actions are being formed – just that security is being considered in the SDLC.
For example, an “S-SDLC” could be as simple as having extra security checks through both passive and active code analysis, or it could mean having meetings to establish coding practices. A company could do nothing more than using a software composition analysis tool and still declare they have an “S-SDLC Process!”
Ideally, multiple methods should be used to ensure each organization is securely developing and deploying code.
How to adopt a security-first SDLC approach
To effectively address security concerns, a security-first mindset must be ingrained in every phase of the SDLC. It involves proactively identifying and mitigating potential vulnerabilities and threats, rather than merely reacting to them after deployment. Here are some key elements of a security-first mindset:
Let’s take a look at security in the different phases.
Analysis
It’s important to plan with the objectives of your cybersecurity program in mind. If the desired security features and purpose of the software are not defined, it will be difficult to meet your objectives. A good plan also helps to ensure that the security objectives and purpose of the software are not conflicting.
If the organization is working to meet a cybersecurity compliance framework such as SOC 2 or ISO 27001 then those requirements must be considered as well.
Design
The security considerations from analysis should be incorporated into the design and architecture of software applications from the outset. Threat modeling techniques can help identify potential risks and inform the implementation of appropriate security controls.
During the design phase of the SDLC, information needs to be assessed for what threats may impact the software being developed. If this software is likely to be targeted by a specific attack or group, the security measures detailed in the design phase should be made to reflect that.
Develop
Developers must follow secure coding practices, such as input validation, output encoding, and secure error handling, to prevent common vulnerabilities like SQL injection, cross-site scripting (XSS), and buffer overflows. Code reviews and automated testing tools can help enforce adherence to these practices.
Before testing can be done on the software through both forms of code analysis, a code review with an additional security focus should be performed. This code review will not only help with ironing out bugs in the software but also aid in the process of discovering any vulnerabilities and ensuring that the concerns outlined in the Analysis step are addressed accordingly.
Test
Thorough security testing, including penetration testing and vulnerability scanning, should be conducted throughout the SDLC.
These tests help identify weaknesses and vulnerabilities that may be missed during development, allowing for timely remediation. For this testing step, including both static analysis with a tool and dynamic analysis by hand would yield the best results for maintaining the security of the code.
Deploy
Proper, secure configuration of servers, networks, and other infrastructure components is crucial to prevent unauthorized access and ensure secure deployment. Implementing secure update mechanisms and regular patch management is also vital to address newly discovered vulnerabilities.
Maintain
A security-first mindset does not stop when the software is pushed out the door! It must also include continuous monitoring of applications and infrastructure to detect and respond to potential threats promptly. Establishing an incident response plan helps minimize the impact of security incidents.
Secure development requires a collaborative approach.
For a collaborative approach to software development to work, members at all levels of the organization must work together and communicate their security concerns and views. An example of this approach would be the engineering and development teams working with higher levels of management to institute policies and methods for the team to follow. Additionally, there is benefit in extending this practice to the selection of tools and modules utilized for software development.
A common mistake in this approach is having only management involved in the approval process for the use of new policies and procedures utilized by the developers working on software development. Without the involvement of the vendor management team, the tools and software used might not meet the standards of the organization. Additionally, senior leadership should be involved in the discussions of the best practices for the development of software that will be used or distributed by the organization.

SDLC for Cybersecurity Compliance
In addition to the security reasons for adopting a security-first mindset, organizations must also comply with a number of security standards and data protection laws.
Security standards, while not required for a secure software development life cycle, can add additional guidelines for the process. With certain standards like SOC 2, particular protocols need to be followed regarding the development of software, such as not utilizing production data in the development environment.
Additionally, policies and procedures may be required based on the security standard or auditor. Failing to prioritize security may result in exceptions being found during an audit. With the need for security trust in the modern age, exceptions found in the SDLC of the organization may make potential clients reconsider their vendor choice.
Conclusion
It may have been Packagists’s responsibility to protect users of its platform from having potentially-malicious code pushed to them. But it’s also the responsibility of developers to make sure they aren’t using potentially-dangerous code in their software. A security-first SDLC process could have either prevented the use of abandoned packages or caught and flagged changes in those packages before they’re pushed to deployment.
If your organization produces a software product, your cybersecurity program is not complete without a security-first SDLC process. Having a real S-SDLC will help to protect your product from being compromised, which helps to protect you and your customers.
Want to get great cybersecurity content delivered to your inbox? Click here to sign up for our monthly newsletter, Tales from the Click.