
Your growing company is hitting a sales plateau – it’s becoming difficult to close deals with security-conscious customers. Your sales and technical teams are getting bogged down with cybersecurity questionnaires and questions about a “SOC 2.” You need to know how to get a SOC 2 certification to remove this roadblock that your company faces.
This guide will give you as much information as possible to get you started on your road to SOC 2 compliance.
What is SOC 2?
Service Organization Controls (SOC) 2 is an information security compliance standard maintained by the American Institute of Certified Public Accountants (AICPA). It’s designed to test and demonstrate the cybersecurity of an organization.
What is SOC 2 Compliance?
To get a SOC 2, companies must create a compliant cybersecurity program and complete an audit with an AICPA-affiliated CPA. The auditor reviews and tests the cybersecurity controls to the SOC 2 standard, and writes a report documenting their findings.
The resulting SOC 2 report facilitates sales and vendor management by providing one document that sales teams can send to potential customers for review, instead of working through cybersecurity questionnaires.
As cybersecurity becomes an increasingly large business concern, merely having a SOC 2 becomes table stakes for selling to many large enterprises. Many companies will refuse to do business with vendors that don’t have a SOC 2 or will sign contracts with written demands that a company will become SOC 2 compliant by a certain date.
One more thing: despite it commonly being referred to as a “SOC 2 certification,” SOC 2 is an attestation. SOC 2 auditors do not certify that a given company has met the standard; instead, the report attests to what they’ve observed in the organization’s security program.
This distinction may seem semantic, but it is significant. SOC 2 compliance is much more freeform than an actual certification like ISO 27001. Companies have more freedom in what controls to pick and implement to secure their company with SOC 2.
We will use both terms in this piece to reflect how people speak and think about this topic.
New! You can ask Fractional CISO Rob Black, our IoT Security Guy/Boston Virtual CISO your SOC 2 questions in this interactive video!
What is the Difference Between SOC 1 vs. SOC 2 vs. SOC 3?
Service Organization Controls (SOC)
| SOC 1 | SOC 2 | SOC 3 |
| Internal controls over financial reporting | Internal controls over information systems | Internal controls over information systems |
| Detailed report | Detailed report | Summary report; marketing purposes |
The AICPA also has two other SOC reports they issue: SOC 1 and SOC 3.
SOC 1
SOC 1 is about controls over financial reporting and is not particularly relevant to cybersecurity.
SOC 3
SOC 3 covers information security just like SOC 2 does, but it is just a summary report of an organization’s cybersecurity program. To get a SOC 3 report, an organization must have had a SOC 2 audit.
The SOC 3 report does not include any confidential information about an organization’s controls and is generally sparse on details. It is not nearly as comprehensive or valuable as a SOC 2 attestation, but it can be published publicly and distributed without parties needing to sign an NDA.
How to Get a SOC 2 Certification: Pick Your Variables.
There are several decisions an organization pursuing a SOC 2 certification must make.
First, it must decide whether get a SOC 2 Type 1 or a SOC 2 Type 2. Then, it must decide which of the five Confidentiality Trust Services Criteria to include in the scope of its audit.
Let’s make these decisions simple for you: We recommend getting a Type 1 for your first audit. For Trust Services Criteria, which ones you select will depend largely on your organization’s service. We’ll give more detail on both of these decisions now.
SOC 2 Type 1 vs Type 2
You pursue two different types of SOC 2 reports: SOC 2 Type 1 and SOC 2 Type 2.
The difference between the two of them is three-fold:
1. The Period of Time over Which the Audit Was Performed.
A SOC 2 Type 1 is a point-in-time evaluation. A SOC 2 Type 2 evaluates the security program over a period of time.
2. The Nature of the Audits.
A SOC 2 Type 1 evaluates the program’s design, while a SOC 2 Type 2 evaluates the program’s execution
3. The Required Evidence.
A SOC 2 Type 2 requires collecting sampled evidence over the audit period, while a SOC 2 Type 1 does not.
- A SOC 2 Type 1 reflects the cybersecurity program as it was on the day it was completed.
- A SOC 2 Type 2 evaluates a company’s cybersecurity over a longer period of time, usually 6 – 12 months. The company must demonstrate to the auditor that it is adhering to its security program throughout this period.
- A SOC 2 Type 2 is more valuable because it highlights a greater level of commitment to security and is more informative about the ongoing state of the security program. A Type 2 audit includes the auditor sampling data throughout the period, evaluating how well the company adheres to its program.
A company with a SOC 2 Type 1 could get its SOC 2 report and then stop upholding any of the controls it says it does.
Should You Get a SOC 2 Type 1 or Type 2?
While a SOC 2 Type 2 is much more valuable than a SOC 2 Type 1, it’s still worth getting a SOC 2 Type 1 first if your company is pursuing cybersecurity compliance for the first time.
Completing a SOC 2 Type 1 audit takes considerably less time and money than a SOC 2 Type 2 audit. Achieving a SOC 2 Type 1 first will help your organization build the skills and practices necessary for ongoing compliance. The lessons learned from the first Type 1 audit will help ensure the more impactful Type 2 audit goes smoothly.
Completing a SOC 2 Type 1 will give your company something to show for your security efforts earlier, and many security-conscious vendors will be happy with a SOC 2 Type 1 report in the interim as long as you plan to get your Type 2.
SOC 2 Trust Services Criteria
As if the choice between a Type 1 and Type 2 wasn’t confusing enough for first-time auditees, SOC 2 has more complexity in the form of its five Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy.
Each criterion is best considered an area of focus. Organizations getting their SOC 2 must select which of the five criteria they will cover in the report.
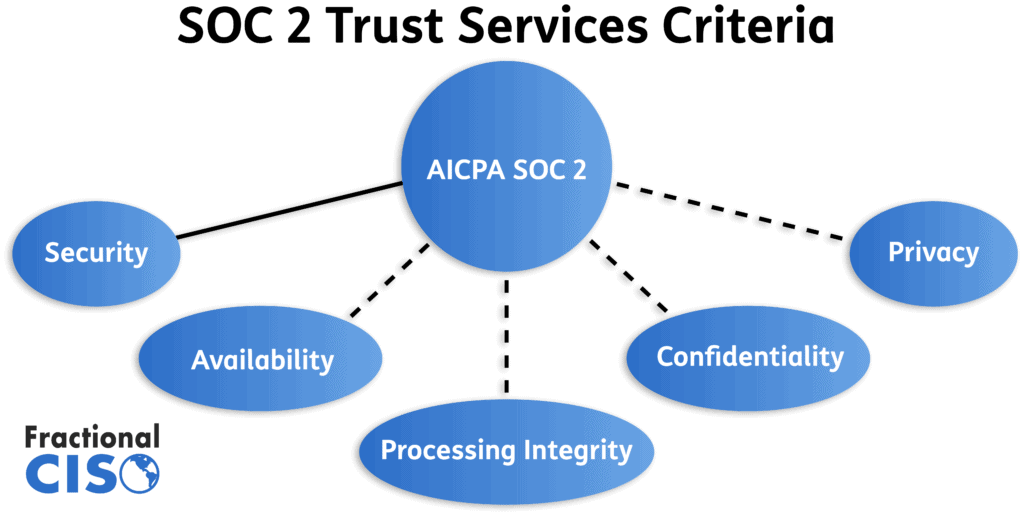
Here’s a quick summary on each of the of the criteria:
SOC 2 Security Criteria
- Security is the only required criterion, all SOC 2 audits must cover it.
- Security is the largest criteria with the most required controls.
- The criteria include SOC 2 guidelines on company management and culture, risk assessments, communication, control monitoring, and cybersecurity strategy.
SOC 2 Availability Criteria
- Availability criteria are all about the uptime of a vendor’s service.
- Availability controls include plans to maximize uptime and restore availability after an outage.
- Business continuity, data recovery, and backup plans are all important controls for this criteria.
SOC 2 Confidentiality Criteria
- Confidentiality covers controls used to keep confidential business data confidential.
- This criteria expects vendors to identify and protect confidential data.
- Example controls for confidentiality include encryption and data destruction.
SOC 2 Processing Integrity Criteria
- Processing Integrity is about how a vendor processes the data it collects.
- Processing Integrity controls are meant to evaluate that data processing is being performed in a consistent manner and that exceptions are handled appropriately.
- It is challenging and laborious work to create the documentation needed to meet these criteria, because it requires SOC 2-specific content with detailed descriptions of how data is being processed. (Almost all other content used in a SOC 2 audit has applications outside of SOC 2, this does not.)
SOC 2 Privacy Criteria
- Privacy covers how personal information is kept private.
- This criteria requires that vendors have a privacy policy, that personal data is collected legally, and is stored securely.
- SOC 2 Privacy is more applicable to Business-to-Consumer companies as opposed to Business-to-Business companies.
Which Trust Services Criteria Should You Pick for Your SOC 2?
All organizations getting a SOC 2 must also include Security and Confidentiality – controls on keeping business data confidential are very important.
Availability is important if your business provides a mission-critical service, and Processing Integrity is important if your service processes a lot of client data.
For Privacy, you are better off following guidelines provided by regulatory programs such as GDPR and CCPA instead of following the SOC 2 Privacy criteria.
A few examples of Trust Service Criteria Selections: Most SaaS companies typically select the Security, Availability, and Confidentiality criteria. For consulting companies, the common choice is Security and Confidentiality. In cases where the company is processing data, they sometimes include Processing Integrity.
How to Prepare for Your First SOC 2 Audit
Preparing for your first SOC 2 audit is no small task.
- Decide on the scope of your audit.
- Identify and fill gaps in your cybersecurity program.
- Create and edit security content (policies and other documentation).
- Modify internal procedures.
- Select an auditor.
- Begin audit.
How to Get a SOC 2 Certification: Scoping your Audit
The first step in getting a SOC 2 is deciding on the scope of your audit.
SOC 2 demonstrates your commitment to security and improves customer confidence in your security program. You should include all services and products you expect customers to have security concerns for.
Most smaller companies will often scope the entire company. As companies get larger and have multiple product lines they must decide if SOC 2 covers the whole company or specific product lines. There can be a huge advantage to having the whole company covered. But of course, if one part of the company is running things looser than the other parts then that could cause problems with your compliance program.
This is also the stage where you will decide between Type 1 and Type 2, and pick which Trust Services Criteria to include.
Identify and Fill Gaps in Your Cybersecurity Program
Once the audit scope is decided, you must evaluate your current cybersecurity program against the SOC 2 control set. Even companies with mature cybersecurity programs do not meet every control from the start.
There are a number of administrative and technical security controls that are often overlooked prior to getting a SOC 2, and they can be sticking points that generate a lot of additional work before and during the audit process – we’ll dive into them later.
Document Your Cybersecurity Program
In order to evaluate your security program, the auditor must have actual items to evaluate!
Unfortunately, it’s not enough to just tell the auditor that you require Multi-factor Authentication for your users. You need to document it in a policy: Who is required to have it? What types of apps are required to use it, versus which ones are not? What authenticator apps are allowable?
Most controls need a policy and evidence that your organization is sticking to the policy created for them. It’s a lot of work – but your company will become much more secure in the process.
How to Get a SOC 2 Certification: Who Performs a SOC 2 Audit?
Not all auditors are created equal. Since the standard is administered by the AICPA, almost any CPA can technically perform a SOC 2 audit, but that doesn’t mean that just any CPA should.
Bad auditors are bad news for your compliance program. To increase the likelihood of a smooth audit and a high-quality report, it’s important to pick an auditor who is knowledgeable about SOC 2 and cybersecurity.
There are a number of things you might consider when selecting an auditor:
SOC 2 Audit Cost
As with any service, it’s important to ensure that costs are covered in the budget and to preserve buy-in for expenses. Remember, you will pay for a SOC 2 Type 2 audit every year going forward!
Experience
You want to select an auditor who specializes in technical audits. Their practice should specifically focus on SOC 2.
Timeliness
You want an auditor who can commit to a time frame to keep everything running smoothly, with key reporting or other benchmarks completed when they are expected.
Readiness Assessment
Some firms provide a pre-planning readiness assessment to evaluate an organization’s readiness for a SOC 2 audit. The auditor should roll the results of this assessment into the audit, and not make you redo all of the work!
If you are working with a SOC 2-knowledgeable consultant, then you probably don’t need the readiness assessment. The benefits of the assessment will be covered by the Virtual CISO services your consultant provides. If you don’t have outside assistance, then the Readiness Assessment will be a very valuable tool.
How Consultants Can Help You Prepare and Complete a SOC 2 Audit.
Preparing for and completing a SOC 2 audit takes a lot of additional specialized work that should fall on a Chief Information Security Officer (CISO) and their team. Few growing companies learning to get a SOC 2 certification for the first time have a CISO or any other built-in resources and talent to complete this work efficiently.
Existing executive leadership, like a CTO, can do a lot. The problem with this approach is that assigning them these cybersecurity and compliance tasks takes away time they could spend on their high-value primary role.
This is why many companies turn to Virtual CISO consultants to assist them with preparing and completing their SOC 2 audit. Virtual CISOs are experienced with SOC 2 and can help with every step from the initial scoping to the completion of the audit itself.
Here’s a small sample of SOC 2 audit tasks that can be given to Virtual CISOs.
- Perform a Gap Assessment – A quantitative risk assessment to assess an existing cybersecurity program and identify gaps that need to be filled to make your company audit-ready.
- Acquire and Implement Technical Controls – IT security consultants help companies add the necessary controls to improve security and ensure compliance if a deficit exists.
- Adjust Policies and Procedures – As we just mentioned, policies and procedures are likely not audit-ready until efforts are made to make them so.
- Create Content – The content created will be key documentation for a SOC 2 audit. Policies, procedures, reports—they can write it and put it in place.
- Project Manage – Virtual CISOs can project-manage the whole audit project. There’s something to be said about domain-expert project managers.
- Perform Risk Assessments – If you were not doing this before, you will now! Risk Assessments are mandatory for SOC 2 compliance, and a Virtual CISO can perform the assessment and write the report.
Picking the Virtual CISO For Your Business – Free eBook
Download the full ebook to learn:
- What the five common types of vCISO providers are
- What specializations each vCISO provider can bring to the table
- The four major points to consider when making your decision
- Perform Vendor Evaluations – Vendor risk management is a part of every SOC 2 compliance program. If it is not already in practice at an organization, it can be valuable to outsource the activity to an expert.
- Perform an “External Internal Audit” – Internal audits are necessary for SOC 2 compliance. They help ensure that your company does everything needed before the auditor catches you. Some firms don’t have an internal audit function, so an “External Internal Auditor” who is familiar with the standards and can keep the organization accountable is helpful.
(“External Internal Auditor” might sound like an oxymoron, but who doesn’t love jumbo shrimp?) - Select an Auditor – A good Virtual CISO will know what makes a good SOC 2 auditor and can remove auditor selection from your plate.
- Advocate on Your Behalf with the Auditor – Your Virtual CISO will be with you for every audit call. They will advocate on your behalf, ensuring the auditor sets realistic compliance expectations for your organization.
Common Tripping Points/Challenges to Getting a SOC 2 Attestation
Administrative Controls
Administrative controls are where most companies fail to comply with SOC 2 physical security requirements. Sometimes, the controls aren’t in place at all (usually this is rectified before the audit begins). Other times, mistakes are made where certain policies or procedures are not carried out correctly.
Either way, learning how to get a SOC 2 certification includes learning a lot about administrative security controls
Access Control
Access control concerns who has access and each user’s level of access. Items may include permissions, account status, and tiered access.
You will need to review your key systems’ access control. This will include your Identity and Access Management (IAM) system, cloud services, networking equipment, servers, VPNs and anything else that is important.
Reviewing clients’ systems regularly finds users that don’t belong. You need to check this before you begin the audit and be vigilant about maintaining it, or the auditor will catch it and you will get an exception.
Change Control
Another important aspect of the audit process is change control. Every change needs to be properly documented.
For the purposes of SOC 2, this involves documenting changes to software, configuration, networking or customer requests.
How do you consistently document changes? A ticketing system!
A ticketing system is one of the best ways to ensure consistent and thorough documentation of every change. Most software companies have to ticket down for software changes but do not apply the same practices to configuration, networking, or administrative privileges changes. This is necessary to implement for SOC 2 compliance!
If you make firewall rule changes, for instance, you should document them in a ticketing (or other) system.
Risk Management and Vendor Management
It’s crucial to start a vendor risk management program for a cybersecurity program. Measuring risk and managing vendors will be part of every SOC 2 audit, no matter how it is scoped.
For the same reason that your customers ask you for details about your security program, you must ask your vendors about theirs.
You need to make sure that your vendors performing key functions don’t compromise your customers’ data upstream. They might have been the ones who got compromised, but who will your customers blame for trusting their data to an insecure vendor?
You need a program to monitor your suppliers. This program should be differentiated by vendor—you don’t need to spend the same amount of time on your paper towel vendor as you do on cloud vendors that process your customer’s data.
You must also perform, write, and maintain a risk assessment for your organization. It needs to be part of a formal process for your management team to make deliberate decisions about risk. They will want to decide whether to avoid, mitigate, transfer, or accept the risk.
It’s important to have a customized risk management setup because every business is different. What works in one industry will not work in another. That is why you will need a program inside your organization to manage risk.

Internal Audit
There’s also the need to have internal audit structures in place.
The idea is that even without an outside audit, somebody monitors and evaluates internal controls.
The most important element here is that the internal auditor has to be independent.
Why? Well, the key question is this: “Would the internal auditors feel pressured not to present findings because their boss would be unhappy?”
If the answer is “yes,” then they are not truly independent. The internal auditor cannot care about the consequences of their findings, they must care only about factually reporting their findings.
Test yourself in this role: If your boss, buddy, or teammate has to remediate the findings or would be embarrassed by deficiencies in their work, then you are probably not an independent auditor.
This is why an “External Internal Auditor” can be very helpful!
Incident Response
Controls are used to respond to specific cybersecurity incidents. These controls are essentially your response and recovery plan for how your firm handles unanticipated threats and breaches. The problem with many companies is that they have a plan that is not detailed enough to adequately respond to and recover from an incident.
The best way to prepare for common incidents is to have a step-by-step plan in place if an incident occurs. These steps for staging an event should include preparation, damage control and analysis, containment, eradication and recovery, complete with a thorough post-incident research and all enhancements.
It is essential that these plans be practiced regularly to account for the various complexities of real-life incidents and provide a comprehensive incident response. The most common form of Incident Response practice is a tabletop exercise.
Outside relevant regulators or third parties should also be informed by detailing other important response areas. Your plan should include who you will bring in to help with a technical breach response, solutions, and a complete analysis of how the incident occurred.
A good Incident Response plan can prevent a cybersecurity incident from becoming a cybersecurity disaster. If a company does not have proper technical expertise in place prior to a breach or incident, any incident will likely become disastrous. This is why it is essential for companies to have technical expertise prior to incidents occurring.
Technical Security Controls
A SOC 2 audit involves many technical controls. Technical controls receive considerable attention in early-stage security programs, so many organizations have several in place before beginning a SOC 2 compliance project. Here are a couple that they often don’t have in place.
Vulnerability Assessments & Penetration Tests
It is common practice for companies to evaluate their organization’s vulnerabilities. Most cybersecurity professionals agree that it is best to evaluate your firm’s entire infrastructure continuously. A complete assessment includes laptops, servers, network equipment, applications, and all devices connected to the firm’s network. Penetration testing is required to get the complete picture.
Vulnerability evaluation is an essential part of your daily cybersecurity procedures. If your organization fixes what it finds, it will lower your firm’s cybersecurity risk.
From a SOC 2 perspective, monitoring for and detecting vulnerabilities, threats, and attempted attacks is important. Penetration testing helps identify control deficiencies, while vulnerability scanning helps organizations comply with monitoring and detecting requirements.
System Logging and Monitoring
The other SOC 2 Technical Control that we are covering here is the logging and monitoring of your company’s systems.
It is critical that organizations log all key security events. However, this is pointless if all you do is create automatic logging but never actually monitor what goes into the logs.
To actively avoid potential complications, organizations should constantly monitor their infrastructure and applications for inconsistencies.
What is a SOC 2 Audit Process Like?
External cybersecurity audits are actually more collaborative than you would think. Most auditors don’t sit down with the intention of busting your company on every little thing you’ve done wrong. They usually want to see the companies they work with succeed and sometimes provide help and advice to get them there.
Before COVID made work remote, an audit was typically a very intensive, short period of time where the auditor was on-site.
Remote collaboration has slowed down the audit process somewhat. An audit usually starts with a kick-off call with the auditor and key stakeholders at the company present. A plan is created for how the audit will proceed that everyone agrees to, and work begins. Evidence is collected and submitted to the auditor, who reviews it. Once all are collected, a report is created.
How Much Does it Cost to Get a SOC 2 Certification?
Everyone knows going in that a SOC 2 isn’t going to be free…but how much does a SOC 2 certification cost?
The answer is simple: it depends!
There are multiple variables that go into the cost of getting a SOC 2.
SOC 2 Certification Cost
Auditor Costs: SOC 2 Audit costs can vary widely. For small-to-midsize firms, expect an annual auditor charge of $15,000-$50,000 depending on the scope of your audit, the size of your firm, and the brand of the auditor.
We have not seen a quality audit performed for less than $20,000, but it is possible that some exist.
Time and Effort: Many clients ask us how much their time and effort will cost. The answer is the same… it depends!
Do you have a great security program that just needs validation or are you building everything from scratch? The former is going to be a lot less work than the latter.
How Long Does it Take to Get a SOC 2?
Mid-sized companies should expect a team of three employees to spend 3-5 hours per week each for six months to prepare for their first SOC 2 audit.
You likely need to factor in other costs as well. For instance, do you already have a ticketing system (or similar system) for tracking change control? If not, there will be an implementation cost for that service.
Do you do a great job of checking access controls already? Then don’t worry about that one. Do you have policies in place, approved by management, understood by employees, and lived by the whole company? If yes, no work there.
For companies undertaking this process for the first time, it’s more than likely that there will be a considerable amount of work to do.
It is possible to put together a cost estimate using this information, but only people with information about your organization can determine its cost.
We Successfully Got our SOC 2 Certification! Now What?
Congratulations on getting your SOC 2 Attestation! Assuming you have a great report with no exceptions, it’s time to leverage it to grow your business.
You’ll want to set up a system for distributing your report to existing and potential customers when they request it. Since the SOC 2 report contains confidential information about an organization’s security program, requesters must sign an NDA before receiving a copy.
Depending on the scale of your business, there are different ways to go about this. You can create a form on your website for people to submit a request so that someone internal will be alerted to the request and can facilitate the process. You can also leave it to sales to handle it so that you only distribute to customers in the pipeline.
Large enterprises have many compliance documents and have purpose-built tools to facilitate their distribution, like AWS Artifact. Midsize ones may use third-party vendors for the same process.
You should also direct your marketing team to include your SOC 2 compliance status in your marketing materials! Having a good cybersecurity program is a differentiator that will put you at the top of any security-conscious customer’s vendor consideration list. Understanding how to read a SOC 2 report will help you understand what potential customers will be looking for in it, and help your team communicate better about your report.
On the actual security and compliance front – just getting a report is not the end. You will move into maintaining and further developing your security and compliance program as needed. At the very least, you will want to transition your program into maintaining annual SOC 2 Type 2 audits. You do not want to lapse in continuous audits, cybersecurity moves fast and a report older than a year will fail to impress any customers performing vendor management.
How Long is a SOC 2 Certification Good for?
SOC 2 Certifications are good for 12 months. This helps to ensure that controls are being properly implemented over time.
Get SOC 2 Compliant with Fractional CISO!
Achieving a SOC 2 is no small task, so this guide has been no small task! We’ve tried to include as much information as possible to teach you how to get a SOC 2 certification, and we wish you luck on your compliance journey.
If you need more hands-on help with your SOC 2 effort, Fractional CISO is here for you as well. Our Virtual CISO services have helped dozens of companies become SOC 2 compliant, reducing risk and growing their businesses as a result. To get in touch, visit our contact page.
Frequently Asked Questions About SOC 2
A SOC 2 compliance checklist is a tool that helps companies ensure they are meeting all of the requirements of the SOC 2 compliance framework.
SOC 2 has 5 sections also known as the “Trust Services Criteria.” They are Security, Confidentiality, Availability, Processing Integrity, and Privacy.
“Certification” is a common misnomer when it comes to SOC 2. There actually is no such thing as a “SOC certification.” Instead, SOC-compliant companies get attestations.
SOC 2 does not prescribe a set number of controls. Instead there are a number of requirements which can be met by as many or as few controls as your company needs.
A SOC 2 security assessment can test your company’s existing cybersecurity program to see how close it is to being ready for SOC 2 compliance.




