There’s a fundamental shift happening in cybersecurity: leading organizations are moving from qualitative, color-coded checklists to quantitative risk models that actually measure risk in dollars and probabilities.
When you can measure security, you can truly improve it.
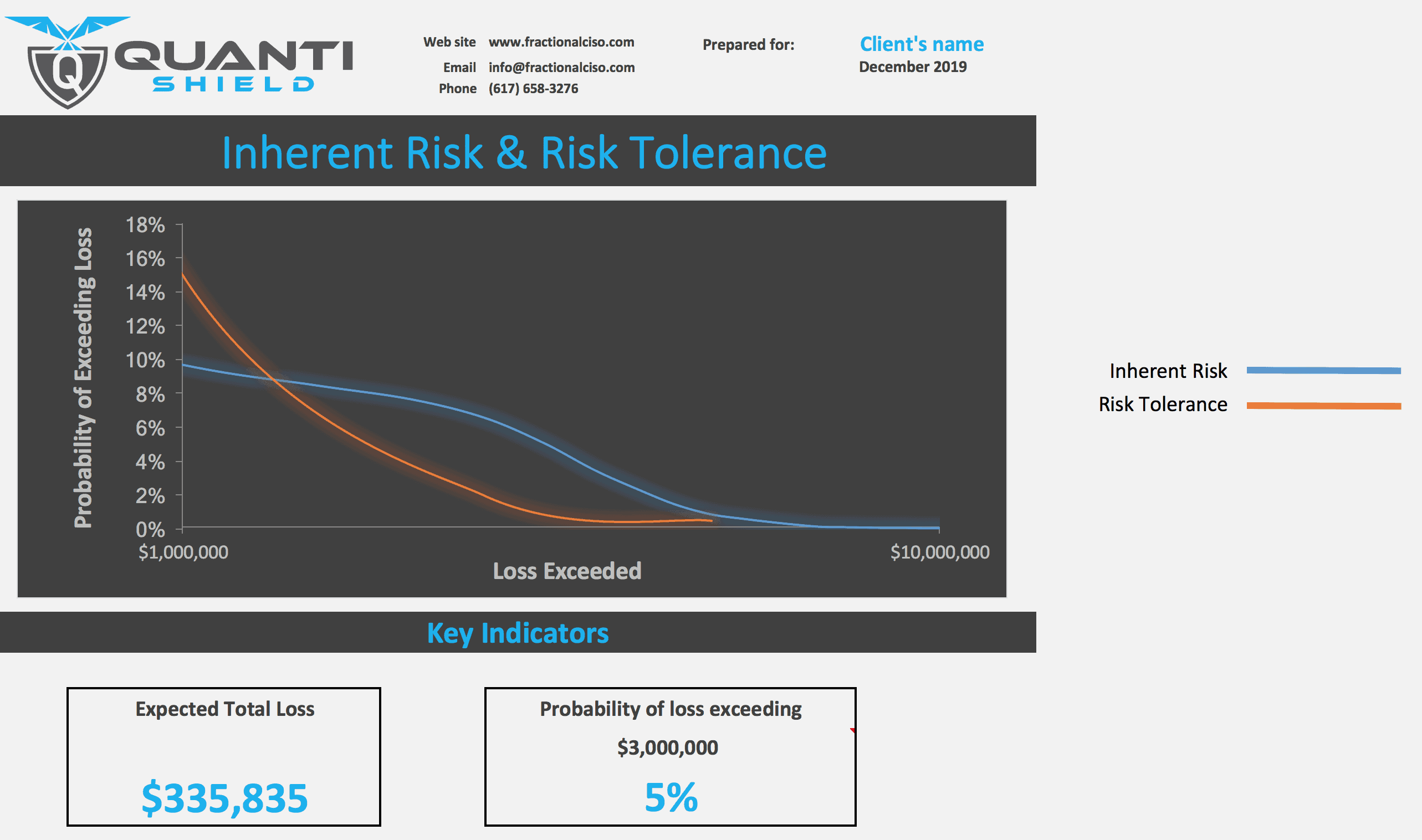
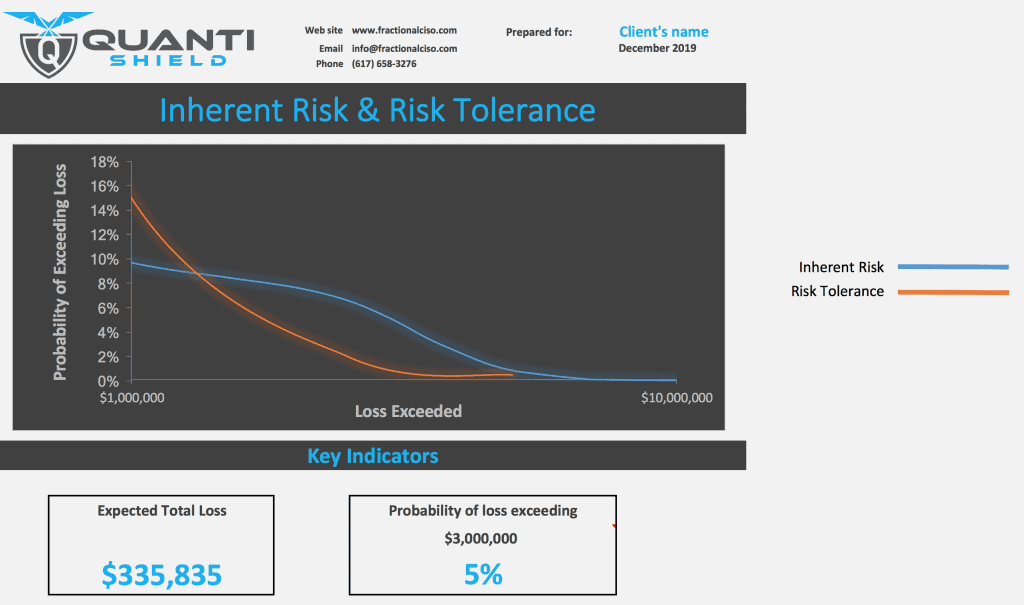
Quantitative cybersecurity risk assessments combine real-world data (even when it’s limited) with proven statistical methods to produce a realistic picture of risk. They answer the two questions that matter most:
- How likely is a damaging event?
- How much would it cost us if it happened?
This approach replaces guesswork and opinion with transparency. When stakeholders disagree, a quantitative model quickly reveals the exact assumption driving the difference—whether it’s about threat frequency, vulnerability likelihood, or financial impact. From there, meaningful, fact-based discussions can take place, and organizations almost always reach alignment on what deserves priority.
Even when deep disagreements persist, you can run “what-if” scenarios in minutes to explore a range of possible outcomes. More often than not, this leads to consensus and a clear, defensible path forward.
The result? A short, prioritized list of the few risks that truly matter—usually just two to four issues that account for the majority of potential financial exposure. By focusing budget and effort here, organizations get maximum risk reduction for every dollar invested.
“Wait—you said there wouldn’t be math!”
Relax. The math is handled for you.
Good tools and the right expertise do all the heavy lifting behind the scenes so leadership can stay focused on business decisions—not Monte Carlo simulations.
One critical ingredient many traditional assessments completely miss: the real business value of your assets. Too many frameworks obsess over technical controls while ignoring the financial consequences of a breach. That’s like building a perfect alarm system without knowing whether you’re protecting a bicycle or a vault of gold.
At Fractional CISO, we fix that.
Our QuantiShield cybersecurity risk assessment blends the best of two gold-standard approaches:
- The rigorous taxonomy and disciplined structure of the FAIR model (the de facto industry standard used by Fortune 500 companies and governments)
- The practical, intuitive techniques from How to Measure Anything in Cybersecurity Risk by Douglas Hubbard and Richard Seiersen
The original FAIR process is excellent—but for many large enterprises it costs hundreds of thousands of dollars and takes months. Most mid-sized organizations simply can’t afford that.
QuantiShield delivers the same level of precision and defensibility at a fraction of the cost and time, making true quantitative risk management accessible to growing businesses.
The outcome for our clients is simple and powerful: a clear, prioritized roadmap that measurably reduces material risk—without breaking the bank.
Stop guessing. Start measuring. Get the insights you need to protect what matters most.
Ready to strengthen your security and win more business? Fractional CISO services can boost your growth while keeping your organization secure. Learn more about our customized vCISO services today.