The first passwords I used as a kid all featured my first and favorite Pokémon, Mudkip.
Sometimes I would include a number (mudkip96), or a number, uppercase, and a special character (Mudkip96!), but the passwords all featured my favorite fictional axolotl nonetheless.

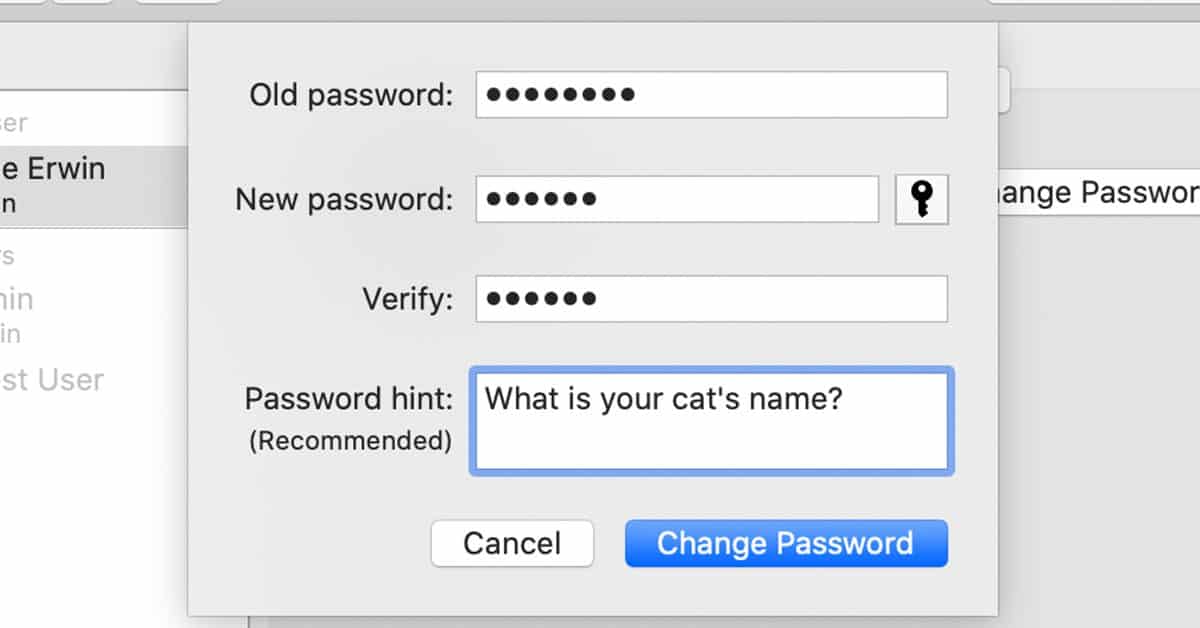
It was easy to remember and if I ever did forget, the password hints “What is your favorite Pokémon?” would always be there to help me remember! Unfortunately, password hints are just as helpful for would-be-attackers as they are for you.
One day, my little brother was able to guess my password to “hack” into my laptop.
Thankfully, he didn’t have any malicious intentions. He just needed to print an assignment for school while I wasn’t home – and it’s not like a 12-year-old has bank accounts or sensitive documents that could be stolen anyways. Still, it counts as an account compromise.
Vector of attack? Password hint.
Password hints help your attackers too.
When you create a password with a piece of information about your life – as most people do so they can remember the password – you are giving attackers another way in. A brute force attack is a waste of time if the attackers can just accurately guess the information relevant to you.
The attackers don’t have to actually know anything about you, or be family, to succeed with this method either. Not with the social Internet.
Say you have a pet dog, Shadow. You really love Shadow and you’ll never forget the day you brought him home, December 12. You can incorporate both of those into a nice, easy-to-remember password. You can even include a vague hint that should be enough to remind you without being too specific.
Password: Shadow12
Password Hint: Doggie
Perfect, right?
Well, considering the fact that you’re reading an article about how accounts are compromised by way of password hint, the answer is obviously no!
You love your dog so much you made the following post to Twinstabook.
“Happy ‘Gotcha Day’ to my favorite pupper, Shadow! Can’t believe he’s been in my life for five years now.”
December 12, 2019
That’s enough information for bad guys to guess your password. Worse yet, if you’re like most users, you have a variation of that same password on most websites. Now multiple accounts have been compromised.
XKCD Encryptic: Turning a Breach into a Crossword Puzzle
Password hints are also a liability in the event of a data breach, as Adobe and Adobe users painfully discovered during a data breach that released details for over 153 million accounts in 2013 – including password hints.
Clues intended to help users maintain access to their accounts became shortcuts for attackers to gain access either through simple guesswork, or by giving their brute-force password guessing programs a set of parameters to work within.
For less-malicious people who try to find the games in life, the password hints became a crossword puzzle.
While xkcd author Randall Munroe was inclined to pick silly hints for entertainment purposes, the actual passwords and hints this breach revealed were no laughing matter. The breach cost millions of users their security and credit card data, and it likely cost Adobe millions of dollars to clean up. Plus, the most commonly used passwords are shockingly easy to guess, especially with hints.
Someone was inspired by this xkcd comic and created 10 actual crossword puzzles using passwords from the 1,000 most commonly used passwords in the breach. The clue for each blank is up to 50 of the most commonly used hints for each password.
The crossword puzzles are fun and you can play them here, but the fact that it works at all is frightening from a cybersecurity standpoint. I won’t ruin all 10 puzzles, but there are a few commonly-used passwords and hints worth highlighting.
One concerning combination was this:
Password: asdasd
Most Common Password Hints: asd, dsadsa, asdasd1, asdasdasdasd, easy, keyboard, usual
There is a nonzero number of people using “asdasd” as their usual password and saying as much in their password hint! They’re attaching their credit card information to this account – and likely storing other valuable information between this password too! It shouldn’t take a cybersecurity professional to tell you that this is a bad practice.
Here’s another common password:
Password: shadow
Most Common Password Hints: dog, cat, pet, horse, hedgehog, pet’s name, dog’s name, doggie, dark, usual
Using a pet’s name as a password is a common practice, and it turns out Shadow is a very common name for dogs, cats, and even horses. Again “usual” turns up – confirming the common malpractice of password reuse.
Here’s a veritable classic:
Password: password1
Most Common Password Hints: password, pass, pw1, usual, passwordone, obvious, my password, facebook, regular, same as always.
Here’s a piece of cybersecurity advice: never use “password” in a password!
Unfortunately, the most common user behavior is to follow the path of least resistance. This means easily-memorized passwords, used repeatedly with minimal variation. While some people use vague password hints, others go so far as to literally stating the password in the hint.
Many users will even reuse passwords they created for personal accounts when signing up for business-related services. Imagine if one of your employees used “password1” or “asdasd” for all their personal and business passwords: now a customer-facing data breach could lead into a business account compromise.
What is to be done about password hints?
The unfortunate truth is that millions of people use weak passwords and reuse them for almost every single service or account they sign up for – and that goes for personal and work accounts alike.
The best way to handle this issue is to throw out password hints and user-generated passwords altogether. While we can’t change the foundation of password-based account security, we can use tools to build a better system on top of it.
Goodbye password hints, hello password managers.
A password manager is any tool that saves passwords for later re-use.
Bad passwords are short, simple, easily-guessable, and reused. Good passwords are long, complex, and never reused ever.
Examples of bad password managers include: a Microsoft Excel spreadsheet titled “passwords,” and a notebook in which you write all of your passwords down. While both of these methods might make it easier to remember complex passwords, they don’t make them easier to type in. The Excel spreadsheet isn’t very secure itself, and they’re also just inconvenient enough that users will feel compelled to slip back into bad habits.
On the other hand, great password managers are dedicated programs or services that make it much easier to use good passwords, from start to finish.
They accomplish this with features such as secure password generation, so the user doesn’t need to invent some weird (but secure) string of text, numbers, and characters. Then, passwords are saved to an encrypted location so they are secure and can’t be lost (unlike the Excel file or notebook). When logging back in, an autofill feature can automatically populate the right username and password. That way, the user never even needs to remember whatever text string the generator created.
Logging in and staying secure becomes as simple as a couple of clicks – of course users are going to prefer that to trying to remember if they capitalized the P in “Password1” or not!
Company Password Policy
If you are a business leader and are concerned about the threat password hints and password reuse pose to your company, you can mitigate the threat by creating a good password policy.
A good password policy should require the use of a password manager and ban the reuse of passwords, especially the reuse of personal passwords for business accounts.
At Fractional CISO, all users are required to use a password manager to create and store their passwords. Password reuse is not permitted, and it’s easy to avoid. Password managers are not a one-size-fits-all type deal, and there are lots of great options out there to consider for the needs of your business.
You should also require the use of multi-factor authentication for every account or service that allows it. That way, users should catch any suspicious login attempts before damage can be done.
Even if you’re not a business leader, you should definitely follow all this advice to keep your private information secure too!
The Bottom Line on Password Hints
While Pokémon fansites don’t tend to store credit cards, social security numbers, or secret business data, tons of websites that hundreds of millions of people use every day do. Frighteningly, their minimum security and authentication requirements probably aren’t that different!
Pick a username, pick a password, add a password hint, and/or add recovery questions. (Recovery questions, by the way, aren’t secure either.)
Practice better security than a 12-year-old! Don’t use passwords so easy that anyone can guess them. Do use a password manager to create secure passwords and never reuse them.
Now if you’ll excuse me, I’m off to have a Pokémon battle with my brother.
Want to get great cybersecurity content delivered to your inbox? Sign up for our monthly newsletter, Tales from the Click! https://fractionalciso.com/newsletter/
Permission to reprint xkcd comic is generously provided under https://xkcd.com/license.html Thanks, xkcd.
Permission to use the photo of the axolotls is provided by the Creative Commons Attribution 3.0 license.