Starting the workday in pajama pants at the kitchen table might be the coziest part about working from home, but the wireless connection between your work laptop and personal router that makes Mondays easier brings some security issues to the table. Your home network doesn’t exactly have the backing of the company’s IT and security departments, after all.
Personal and professional devices need different levels of security. Bad guys are more likely to be interested in business networks with high-value data, instead of residential networks used primarily for entertainment and communication. Thanks to the COVID pandemic, home network security became much more important now that many of them are transferring important business data.
The general list of security controls for home Wi-Fi looks something like this:
- Use strong encryption (WPA 2)
- Change default SSID
- Change the default password
- Disable WPS (Wi-Fi Protected Setup)
- Update firmware
- Use a guest network
These are all almost universally agreed upon. However, there’s one security control that some recommend and some don’t:
- Hide network SSID
There is a debate within the cybersecurity community as to whether this is a valuable security control for wireless networks. Navigating the ins and outs of computers, networks, and the internet at home is confusing enough on its own without the added confusion of conflicting opinions. So let’s take a look at this argument and see if we can come up with the right answer.
Background: What is an SSID?
An SSID, or Service Set Identifier, is the name of a wireless network. It is broadcast by the wireless network’s router (or access point) so devices can see the different wireless networks in their vicinity. This is what makes it easy for users to find, select, and connect to nearby access points.
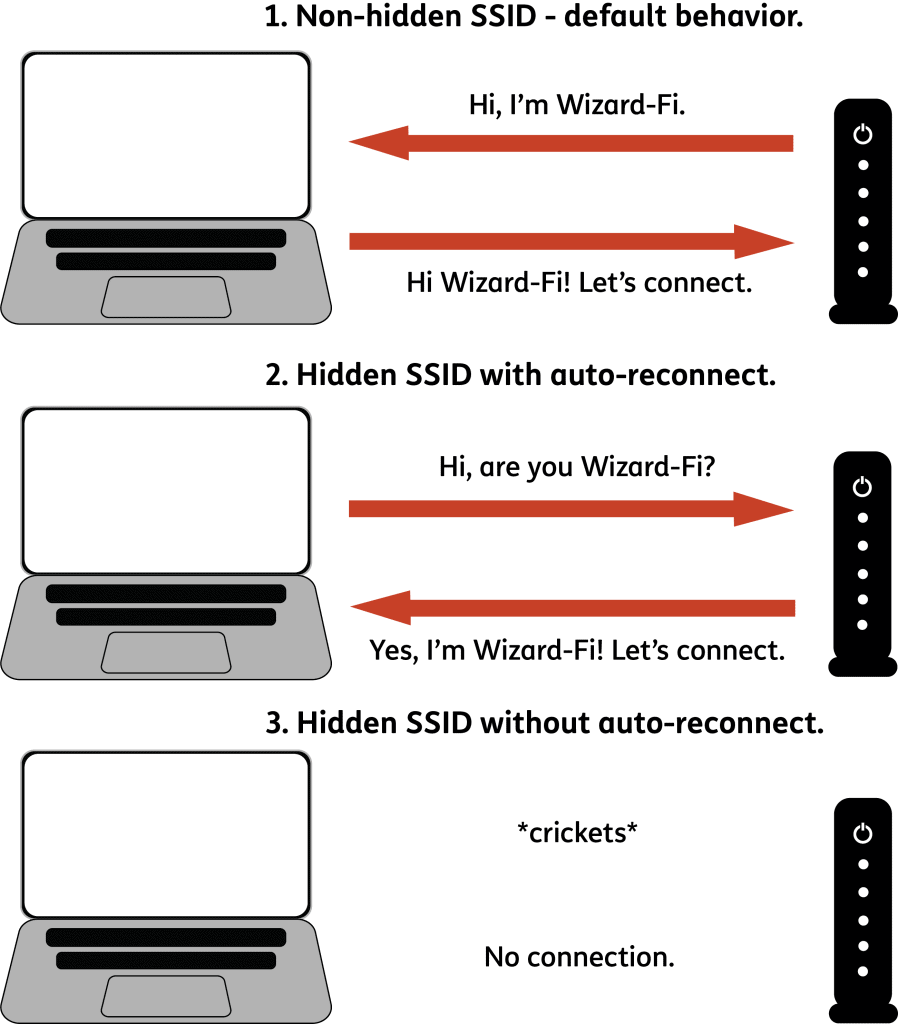
The default setting for a wireless router is to broadcast its SSID.
What is a hidden SSID?
Hiding an SSID is simply disabling a wireless router’s SSID broadcast feature. Disabling the SSID broadcast stops the router from sending out the wireless network’s name, making it invisible to users. However, this only hides the name from showing up on device lists of nearby networks. The network itself is still there, since people still need to use it. This brings us to the debate.
Pros of hiding your SSID.
The primary benefit of hiding your SSID is that it reduces the likelihood of an attack by keeping hackers and nosy neighbors from even knowing your network is there. It makes your network less of a “low hanging fruit” by making it more difficult to find. The theory is that a casual attacker would choose to attack a more obvious, in this case non-hidden, network instead.
However, your network is still there and can still be found by determined attackers. The SSID is included in informational data, or data packets, that are transferred on the network. These data packets can be found and examined with readily available network analyzing tools and anyone with the know-how to use them.
That being the case, hiding an SSID is not a one-and-done solution and must still be coupled with the other Wi-Fi security controls listed above. A hidden network cannot prevent an attack, only reduce the likelihood of one ever happening.
Cons of hiding your SSID.
The main argument against hiding your SSID is as stated above: the more technically advanced bad guys can still find your network whether the SSID is hidden or not. To them, you may as well be running around with a giant sign that says “I use a hidden network!”
Readily available network scanning tools, such as inSSIDer, will report back on all nearby networks, including hidden ones. The screenshot below shows what it looks like when someone detects a hidden network. The eighth listing down with a pink bar next to its name is the hidden network. This app leaves it blank, others will list “Hidden SSID.”
From here, there are a multitude of hacking tools that an attacker can use to identify your hidden SSID. They might even feel encouraged to do so – just what do you have that’s worth hiding?
Another giveaway for your hidden network are your mobile devices themselves. For user convenience, computers and cell phones are always trying to reconnect to your preferred Wi-Fi network. This makes for a seamless experience when you get home, open your laptop, and don’t have to worry about reconnecting to Wi-Fi.
Normally this is handled by the device acting as a receiver – it is listening for a ping with the SSID of the router to establish a connection. When you use a hidden SSID, you shift that responsibility to the mobile device as opposed to the router. Now, whenever your device is away from the hidden network, it’s constantly sending pings to look for the router. The SSID is a crucial bit of information that must be included in the “handshake” between the router and device in order to establish a connection. If neither device is broadcasting, they don’t know that they’re supposed to connect to each other.
An attacker that’s monitoring local network signals can easily detect this behavior, telling them:
- That you use a hidden WiFi network at home or work
- The name of that network
Hiding your SSID comes with another usability drawback too – it makes connecting to your network more difficult for legitimate users. Instead of selecting from a list of visible networks, you have to manually enter all of the network details for your Wi-Fi connection.
Disabling the SSID broadcast also makes it difficult for older versions of Windows to find and hold their connection to a network. These older versions of Windows will prioritize connecting to a network with a broadcast SSID regardless of signal strength, and disconnect from a network without a hidden SSID and connect to one that is broadcast. Wireless dongles have also been known to drop connections when the SSID is hidden.
Our Take on Hidden SSIDs
Both sides of the argument have valid points, so the answer as to which is the better practice ultimately boils down to this question:
Is the benefit of discouraging a casual attacker worth the risk of looking like a more attractive target and complicating legitimate network use?
In our opinion, it’s not worth the drawbacks to hide your SSID. You can discourage casual attackers and hackers interested in low-hanging fruit with other security controls: use a strong password, encrypt your network traffic, and run updated firmware. Unlike hidden SSIDs, these come with no usability drawbacks.
So the answer is NO. The other security controls are enough that the benefits do not outweigh the risks of hiding your SSID – don’t do it!
Other Ways to Protect Your WiFi Network
Beyond the commonly known methods like encryption and SSID settings, there are several other steps you can take to enhance the security of your home or office Wi-Fi security. These can include:
- Ensure that the remote management setting is disabled unless it’s absolutely necessary. Doing this will ensure that changes to your router’s settings can only be made from a device that is currently connected to the network.
- Regularly audit the connected devices to make sure there are no unknown devices leeching your connection.
- Consider segmenting your network. You can create separate networks for different devices (ie one network for your personal devices, one for your smart home devices, one for guests, etc). This will limit the damage a potential intruder could cause if they only gain access to one segment of your network.
- As always, be wary of phishing attempts or suspicious links, as sometimes, these can compromise network security.
Taking a multi-layered approach to security is always the most effective way to protect your WiFi and cybersecurity at large.
Final Thoughts
If you want to ensure the overall security of your home or business network, it’s crucial to assess your cybersecurity risks comprehensively. At Fractional CISO, we offer professional cybersecurity risk assessments that can help identify vulnerabilities and provide recommendations to enhance your network’s security posture. Our experienced team will analyze your network infrastructure, evaluate your existing security controls, and provide actionable insights to mitigate potential threats. Protect your sensitive data and minimize the risk of unauthorized access by leveraging our cybersecurity risk assessment service.
To receive more great cybersecurity content for business leaders, sign up for our monthly newsletter: https://fractionalciso.com/newsletter/
Frequently Asked Questions About Hidden SSID
When you have a hidden SSID, the name of your wireless network will not be publicly visible to people who are trying to find a wifi network. However, the network will still exist, so only those who know the SSID name will be able to join by manually entering it.
To make your WiFi network invisible to others, you need to go into your router’s settings and disable the SSID broadcast option. This stops the router from publicly broadcasting the network name. When you hide your SSID, it’s still accessible to people who know the SSID and have manually entered it.
Yes. you can connect to a hidden SSID. You must manually enter the SSID name and password on your device in order to connect to that network. Once you’ve connected, your device should remember the network and reconnect automatically so you don’t have to manually join it each time.