Split tunneling is serious business.
Netflix just dropped the new season of that show you’ve been waiting on for a year, so you must, of course, immediately binge watch it before you see any spoilers. But you also have some work to finish up before tomorrow. While you are great at multitasking, your technology is…not as skilled. So how do you manage this all at the same time? Split tunneling.
Open the laptop, establish a protected uplink to the Organization’s server via the Virtual Private Network, and divide the data streams based on mission-criticality to maximize transfer efficiency. Shamelessly binge Netflix show.
Okay, maybe it’s not that serious, but it offers serious potential for your business. Especially if your employees are working remotely. Given that working from home could become the new normal for many jobs, it’s still pretty serious.
The security control divides the Internet traffic and sends some of it through the encrypted VPN tunnel, but routes the rest through a separate tunnel on whatever network the computer is normally. This makes it possible for users to enjoy the security benefits of the VPN where needed, while bypassing the VPN where VPN access is restricted or otherwise impacts the use of a service.
There are several types of split tunneling that work in different ways:
Types of Split Tunneling
The first two types of split tunneling are based on inclusions – split-include tunneling. All traffic is rejected from the VPN tunnel with the exception of specific explicitly included website and app traffic. This approach will generally route less/a narrower variety of traffic through the tunnel, since the list of inclusions passing through the tunnel will be smaller than the rest of the Internet which travels outside the VPN tunnel.
URL-based: URL-based split tunneling uses URLs to specific websites. With URL based split tunneling internet traffic is sent through the open network and the user specifies the URLs that need to be securely accessed through the VPN. This method is typically implemented by using VPN browser extensions.
App-based: App-based split tunneling utilizes apps to control what internet traffic is encrypted. With app based split tunneling all traffic goes through the open network and the user specifies each application that is accessed through the VPN.
In practice, split-include tunneling is useful for when you only need a few specific connections to be encrypted. For example, an organization would want a remote developer to have a secure connection to its servers so important company assets aren’t being transmitted on the open web.
The third type, inverse split tunneling operates based on exclusions, split-exclude tunneling. All traffic is accepted into the VPN tunnel with the exception of explicitly excluded website and app traffic. Excluded traffic is sent through the open network. This approach will generally route more/a wider variety of traffic through the tunnel, since the list of exclusions will necessarily be smaller than the entire rest of the Internet which passes through the tunnel.
In practice, inverse split tunneling is useful for trusted, high-bandwidth uses, like YouTube streaming. It’s pretty unlikely that malware would be transmitted through a Google website, and the high bandwidth that HD video uses is better off being routed through faster and cheaper general Internet rather than a slower VPN connection with limited bandwidth.
What are the pros?
Split tunneling reduces the usage of limited VPN bandwidth. Only traffic that needs to be encrypted goes through the VPN, so other traffic does not use up VPN bandwidth.
Users will not have latency suffer while using the open network. Even fast, modern VPN services slow latency down somewhat. Split tunneling will increase the speed of all non-VPN traffic.
Users get the best performance of the ISP they are using. Again, VPNs reduce the speed of traffic being routed through them. It allows for max speed for at least some applications and traffic.
Users do not need to connect and disconnect to the VPN as they switch between protected and non-protected activities. This makes access easier and removes a point of potential user error. It can also help to alleviate some usability issues that come with using the same VPN network for all applications, or having to swap for all connections.
High priority corporate traffic will stay high priority. Personal and/or less critical traffic transmitted over the VPN can reduce the speed and bandwidth of high priority corporate traffic. Split tunneling ensures the VPN only carries what your organization deems is important to secure.
What are the cons?
Split tunneling can increase security exposure, especially if your company is running its own VPN. Split tunneling punches a hole in your company’s network security perimeter, which can lead to some problems.
- Security cannot monitor all traffic on a remote client to protect against malware from the general Internet when split tunneling. The remote endpoint’s non-encrypted traffic does not benefit from perimeter defenses from threats such as drive-by exploits, malware downloads, phishing sites, etc.
- Users’ web browsing activity may not be protected by encryption of the VPN connection while using public Wi-Fi or facing man-in-the-middle attacks. There are other endpoint security agents that can/should be used to help mitigate the risk here, but the user is still losing a layer of security for their device when data isn’t sent via VPN.
If the endpoint is compromised through non-protected traffic, the VPN connection gives the attacker a foothold into the company network. Essentially that compromised laptop becomes a pivot point from the public Internet into the trusted segment, bypassing the perimeter defenses.
Auditing of all Internet activity is not possible. Companies lose visibility on remote employees’ internet activities when they aren’t using the company VPN. You can’t see such as using open public wifi networks or browsing forbidden sites on company time. This may also be an issue for security monitoring if you require it from a compliance standpoint.
Setting up split tunneling configurations requires time and expertise. If the configurations are not set up properly and are insecure it can allow malicious actors a way into the network and access data. It can also be hard to separate out the traffic you want encrypted. For example, with a CDN for a live stream event may be allowed to go over an open network, but other types of traffic that should be encrypted, such as chat, are also using the allowed CDN.
Split tunneling provides an avenue for data exfiltration. A disgruntled or malicious employee with some technical knowledge might use it to exfiltrate company data.
Cloud Data Center Split Tunneling
Up until this point, we have been talking about split tunneling for your corporate network. Remote employees have to go through the internet, not the corporate network, to access any data or resources in a cloud environment. If you are connecting your web traffic into your data center then you should always have split tunneling on. You do not want to send your employee’s cat videos and cake pop recipes into your AWS instance hosting client data!
There are cloud-based traffic security solutions available such as a cloud access security broker (CASB) or a secure access service edge (SASE) that can be used to provide VPN access and act as an intermediary to decide which traffic goes where between the cloud resources and the user endpoint.
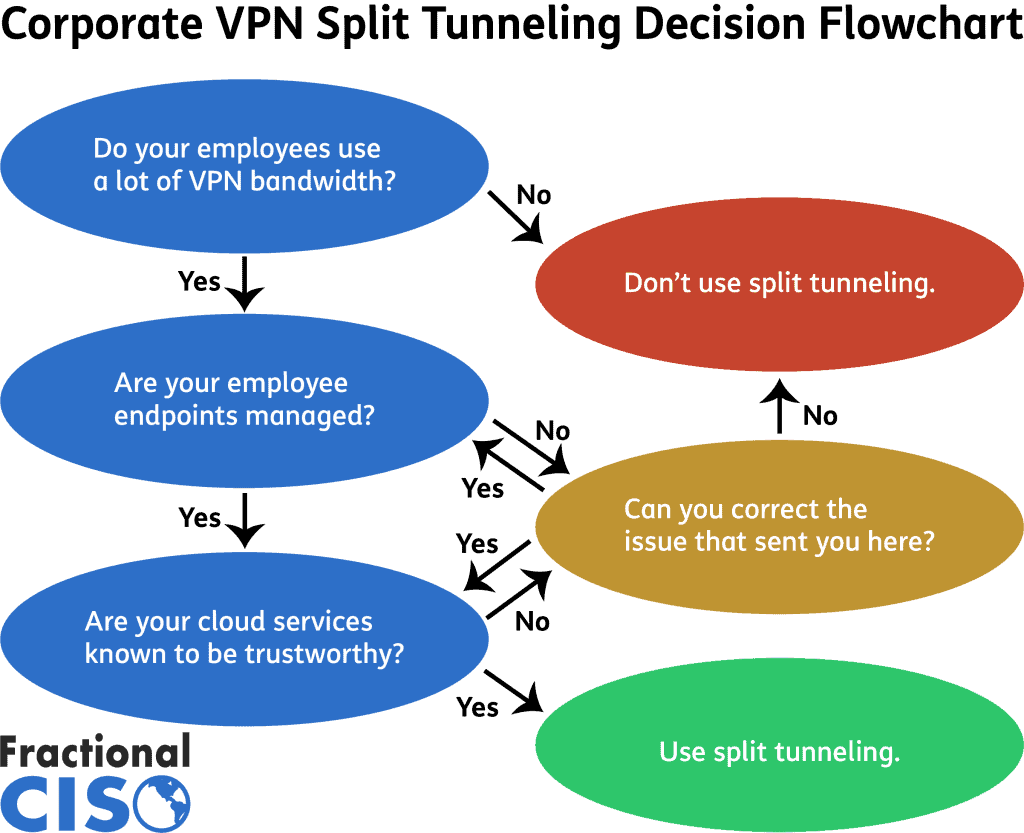
Should your company use split tunneling?
Split tunneling can be a very beneficial control for companies to use, especially if VPNs are critical to their workflows. To help you decide whether or not you should use split tunneling at your organization, we’ve made this nifty flowchart.
When in use, it’s best to exclude high-bandwidth known trustworthy traffic from your VPN. The most obvious example for this is YouTube streaming and video conferencing – like Zoom, GoToMeeting, and Microsoft Teams.
Actually, Microsoft itself has found great success using split tunneling to maximize VPN usability while its 100,000+ global employees are working from home during the COVID-19 pandemic. Because Microsoft inherently trusts Microsoft apps, they could exclude Office 365 and Microsoft Teams usage from the VPN. The exclusion of Teams especially helped make bandwidth available for developers and other employees who needed secure VPN access to Microsoft’s network.
While there are split tunneling success stories, it’s still impossible to issue a blanket “yes” or “no” answer when it comes to the question of whether or not to use split tunneling. Ultimately it comes down to a risk assessment or cost-benefit analysis for each use case to determine whether or not it makes sense for a company to implement the practice.
You should examine each application and use-case. As previously stated, video conferencing apps and VPNs are pretty happy to not get involved. Similarly, full operating system updates are of critical importance. Low bandwidth and lower latency will impact these activities, so the risk of going without a VPN might be worth the higher speed gained as a result. On the other hand, you want your developers to have a very secure connection to your servers and you don’t want their laptops getting compromised, and it does increase that risk.
An organization can also consider using split tunneling in some areas and not others. If a company has separate networks, it might make sense for an organization to use split tunneling for some but not others. For example, the production department might use split tunneling, while the IT department does not. It’s important to factor in the organization’s other security controls too:
Are the remote endpoints managed by the organization? If so, what protections are being used on them?
Is the company using a cloud based traffic management system? These additional security controls may be taken into account to help determine if those controls mitigate the risks of split tunneling.
Split tunneling can be a very granular decision, with it being implemented on a per-user basis.
While split tunneling in practice might not be as dramatic as dividing the data streams based on mission-criticality sounds, its potential poses a unique question to business leaders. There are many factors to consider before deciding on its usage, and as with so many things in cybersecurity, there is no one-size-fits-all solution.
Want to get great cybersecurity content delivered to your inbox? Click here to sign up for our monthly newsletter, Tales from the Click.