Suppose you see a few people in a rented car, parked across a street at a hotel, next to an office.
Does this sound suspicious to you at all? Not at all! Right?
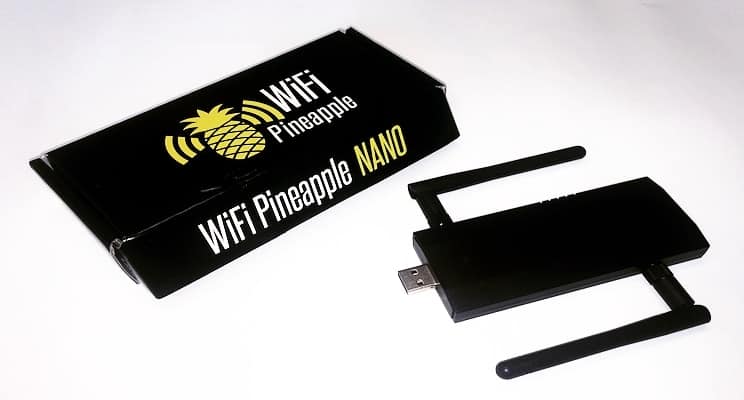
In a real-life version of this story, those people were attempting to perform a cyber-attack on the Organization for the Prevention of Chemical Weapons (OPCW). According to reporting on the incident, Dutch law enforcement foiled their attempts when they discovered their ‘weaponized’ car with long-range high-gain WiFi antennas, battery backup, and power inverter and something that looked to be a WiFi Pineapple kit.
Such “close access” attacks on WiFi networks are well known in the cybersecurity world, as an established technique for penetrating a target. The news of the Dutch attack validates that the threat is real. The WiFi Pineapple just makes it easy to target WiFi access points, as well as employee’s WiFi-enabled devices.

WiFi Pineapple: It’s Not a Fruit
The “WiFi” Pineapple is a pen testing tool, originally created in order to allow IT professionals to test the vulnerability of their networks. They can be used to de-authenticate and spoof a legitimate network, forcing employees to connect to this fake network. Once connected, the attacker can target the local device on the fake network, to exploit it and gain access to its data. This device can be set up as a rogue wireless access point within minutes, ready for attack.
WiFi is Inherently Flawed
A WiFi operation relies on trust, especially in terms of the validity of the source and destination addresses. That is exactly what is leveraged to spoof values and carry out attacks. WiFi obviously presents more challenges than the traditional wired networks, due to the easy accessibility of the signals. The Access Point (AP) generates radio waves traveling through walls and windows, and these waves can be picked up by someone sitting outside in a parking lot!
Any time you connect to a WiFi network from your phone or computer, your device saves that network’s SSID. Remember the auto-connect feature that your phones and laptops have that allows your device to connect to that SSID automatically? It comes at a major cost.
For example, say you connected to the airport WiFi called- ‘Airport WiFi’. After you’ve left the airport, your device will broadcast a signal asking if WiFi access points around the device are ‘Airport WiFi’. Your device does this for any network you’ve connected to in the past.
WiFi Pineapples take advantage of this feature by scanning for all the SSIDs being broadcast by devices in its vicinity. It then rebroadcasts these SSIDs to trick devices into thinking it is an access point that has been connected to in the past. The WiFi Pineapple sees your device asking, “is this network ‘Airport WiFi’?” And then starts broadcasting its own signal that says “Yes, I am ‘Airport WiFi’, connect to me.”
WiFi Pineapple is Not That Difficult
The WiFi Pineapple is available to anyone on Hak5’s website at the price of $99.99. It will be delivered to you within a week’s time and setting up the device takes about fifteen minutes. Downloadable modules and plugins are available for free. Operating this device to launch a basic attack takes minimal formal training or knowledge. To test it out, I tried to launch a basic coffee shop attack. The goal was to capture the login credentials of the victim.
Demonstrating the Basic Coffee Shop Attack
A while ago, obtaining someone’s login credentials was a piece of cake. All that was required was the SSLsplit module. You can find videos on YouTube from 2013-2014, where you can see how easy it was to capture literally any login credentials.
Now, it’s harder, since browsers have adapted HSTS (HTTP Strict Transport Security) to protect websites against downgrade attacks. They also warn users when the site is not secure.


These measures have made attacks like a WiFi Pineapple gambit difficult, but not impossible.
While
SSLSplit is pretty much useless now, it is still possible to obtain credentials
by first launching a de-authentication attack. This forces the user to go
through a captive portal where the attacker will be sitting with their ears on
the door.
With two easy steps using two free modules, the attacker can grab your
credentials.
1. Deauth- With one click, the WiFi Pineapple
can launch a de-authentication attack on clients connected to nearby APs.
Or if you want to kick off all the clients from a particular AP, you can do that too.

2. Evilportal- This is a trap that lets users ‘authenticate’ themselves to connect to the WiFi network.
After de-authenticating, the next step is to direct the victim to the login portal. Creating the login portal was easy, as there are several codebases available online, even ones that are specially designed to be ‘evil portals.’
The login portal I created looks like this-

Once the victim entered their credentials, I was able to capture it in a log file-

Step 2 can also be done using another module, PortAuth, which is basically a clone of captive portals and acts as a payload distributor for the WiFi Pineapple.
PortAuth allows the users of the WiFi Pineapple to easily spoof captive portals and regular websites, capture credentials and system information, and delivers payloads to targets.
This has just scratched the surface of what’s happening around these sorts of technologies. With more training and deeper knowledge of the modules and attacks, the WiFi Pineapple is capable of so much more. It can generate fake certificates, in case anyone needs an extra touch of authenticity. It can also be used to inject raw frames and capture WPA handshakes.


The attacker doesn’t even have to know your SSID! The WiFi Pineapple can collect this information by collecting leaking SSIDs from the potential clients. They are added to the SSID pool and are used to spoof networks and trick devices into connecting to malicious networks.
A WiFi Pineapple Coffee Shop Attack Can Happen to Your Organization
We’ve become alarmingly accustomed to connecting to random wireless access points while we’re out and about. From a security standpoint, that’s a problem.
When the average person at the airport waiting for a flight sees SSID names like ‘Free Airport WiFi’, what are they going to do? Assume it’s an attacker’s honeypot and steer clear of it, or believe it’s free airport WiFi and dive right in? Exactly. Too often, they’re not cautious – with big consequences.
Your company employs a number of employees, including software engineers and others who have a high level of access to the company’s infrastructure. You might also allow BYOD and working from home. It is very much possible that one of these people falls for an attack like this, putting not only their devices, but the whole network at risk.
How to Defend Against the Malicious WiFi Pineapple
Luckily, there are some simple practices you could follow as an individual to protect yourself from getting pwned by a WiFi Pineapple:
- Beware of public WiFi! This goes without saying: only connect to WiFi networks you know and trust. Do not conduct sensitive business, banking or health care-related activities over public WiFi.
- Use a VPN. if you absolutely must connect to a public WiFi, USE A VPN! It is your best bet when it comes to surfing the net securely. A VPN will encrypt your data before routing it to its destination, so even if the attacker is able to see that your device is connected to their WiFi Pineapple, since you are using a VPN, they will not be able to see the data that is being routed.
- Connect to HTTPS only. Most websites that you visit on a regular basis that have sensitive information on them have switched from HTTP to HTTPS. So, if you type just the website’s domain name, you will be directed to the secure HTTPS site. The bad news is, too may websites do not use HTTPS and can leave you open to a WiFi Pineapple attack. So, the best way to stay safe is to check for HTTPS and use a VPN.
- Whenever
you are done using public WiFi, make sure that you configure your devices to
‘forget’ that network. This way, since your device won’t constantly broadcast
the SSIDs of the networks it has connected to in the past, the WiFi Pineapple
won’t spoof the SSID and trick your device into connecting to it.
Keep your WiFi functionality turned off when you are not using it, don’t allow your devices to automatically connect to open WiFi networks. - Be vigilant about your network settings and surroundings. You can’t be connected to ‘Airport WiFi’ if you are sitting at home. Be skeptical of network names like ‘Free WiFi’ and network names for common hotel chains and other franchises.
- Verify that the SSL certificate for the website is genuine and was issued to the company to which you are connecting.
- If you can, just use a wired connection.
If you are the Server Admin or IT Administrator, here are some precautionary measures you could take to prevent your organization from being duped by WiFi Pineapple’s malicious attacks:
- Install a Wireless Intrusion Prevention System (WIPS) on your network. It will keep an eye out for Evil Twins and Client Deauths 24/7 and will automatically detect and neutralize WiFi Pineapple attacks for you.
- Update your WiFi routers, access points and client devices to patch unknown vulnerabilities.
- Use HSTS. This policy forces all server responses to pass through HTTPS connections instead of plain text HTTP. This will ensure that the entire channel is encrypted before data is sent.
Next Steps
In light of the risks posed by cyber-attacks like the WiFi Pineapple, it is crucial for organizations to prioritize their cybersecurity measures. At Fractional CISO, we offer comprehensive virtual CISO services that can help safeguard your company’s infrastructure and data. Our team of experts can conduct cybersecurity risk assessments to identify vulnerabilities and develop strategies for mitigating threats. Take proactive steps to protect your organization by partnering with Fractional CISO.
To receive more great cybersecurity content for business leaders, sign up for our monthly newsletter: https://fractionalciso.com/newsletter/



