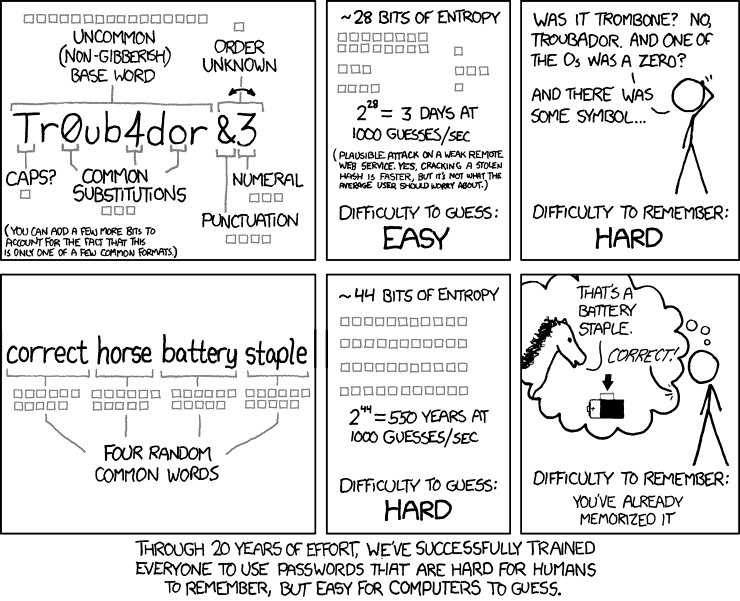
The “Correct Horse Battery Staple” piece at xkcd is still so popular! I guess if you want something to live on then make a comic about it…
In the comic, you have an example of the type of password that we’ve been taught to create by IT systems over the past couple of decades (Tr0ub4dor&3). All of its little nuances are diagrammed to show how complicated it is to generate one of these passwords
In the next two frames, you see that the statistical difficulty of being predicted is relatively compared to the “correct horse battery staple” approach, where using random words makes a password longer and greatly increases the computing power needed to guess it in a brute force attack. Then you have a person using a mnemonic device to effortlessly remember that ‘word-based’ password…
I wrote about how this was an “okay” idea three years ago. (meh) My advice now is largely the same, but several things have changed, so here is an updated Correct Horse Battery Staple Review.
Users Should Not Be Creating Passwords
Part of the problem is that users are still making up their own passwords, which, by and large, is an inefficient and problematic way to do cybersecurity.
Here’s the problem – any time you allow end users to choose their own passwords, many of them are always going to try to dumb it down to make it easier to remember, and no matter what the protocol is, you’re going to end up with relatively weak passwords. That’s why you see so many corporate systems scolding the user when they start to type in a new user-created password – use a special character! Use a capital letter!
Unimpressed by this nanny state password advice, people might put in things like “get into my computer” or “help me login” when they should really be inputting things like “eldritch foster peace mothballs.”
So (as you’ll see in the rest of this Correct Horse Battery Staple review) users should not be creating passwords for the most part. Instead, it makes more sense for companies to be using a password manager.
Password Manager instead of Correct Horse Battery Staple
A password manager doesn’t eliminate password threats, but it does reduce the attack surface for users who might otherwise leave themselves (and the company secrets that they have access to) pretty exposed and vulnerable.
Using a password manager changes user behaviors. It actually takes some of the responsibility from the end user, which is generally a good thing for everyone involved. Most people don’t come to a company wanting to be their own cybersecurity expert – they don’t want to have to be guided into creating their own ideal security apparatus! When they can get help, many of them are grateful for it. As our digital world evolves, we’re moving toward the point where fewer users will be creating and maintaining their own passwords.
If you are not with me on the password manager decision, check out this article. Or Google “password manager” and read advice from many top cybersecurity minds.
A password manager reduces an attack surface significantly for most use cases. The password manager is most effective with these tips:
- pick a unique monster password for your password manager
- never reuse or share the master password. (I mean never.)
When we do create passwords, it should be for the aforementioned password manager. We should also create passwords for our devices. Otherwise, we should delegate password creation and management to our password manager.
Bad Guys Read xkcd Too!
The “Correct Horse Battery Staple” password is now a widely-known concept. That also makes it less effective in some ways.
When creating password dictionaries, bad guys can use Correct Horse Staple Battery style passwords. As a matter of fact, the best password crackers combine dictionary words in their attacks. Ars Technica’s following of Nate Anderson’s newb crack at password piracy is just one example! Can you even believe it is possible to easily crack “”momof3g8kids”?
If you are stuck with the conventional password system, when you need to memorize a password, using a mnemonic device is absolutely good, because computers can’t re-create that kind of thinking. Hackers can program computers to use dictionary words, but they are less likely to excel at predicting the kinds of random things that people can commit to memory using a relational mnemonic device like the one in the comic so you’re usually fairly safe there. Still, there are other problems with the “random word” approach that are concerning.
Correct Horse Battery Staple Review of Dictionary Size
In our previous review, I criticized the dictionary size of “Correct Horse Battery Staple.” It turns out that I was not harsh enough!
According to experts, most adult native English speakers know 20,000 to 35,000 words, but that includes higher-level vocab that might rarely get used when you let end users put in their own passwords. What are the chances that a user-submitted passphrase would be “Grommet Addend Esoteric Tautology”? The evidenced trend is that people are more likely to select from around 3,000 very common words, and that means hackers have a lot fewer combos to run!
Our password complexity with four words at this level of vocab is now 3,000 to the power of 4, or 81 trillion possibilities. If you used a 9-character password made up of 26 lower case and 10 special characters you would have 101 trillion possible passwords. Alternatively, an 8-character password comprised of lower, upper and special characters will have 218 trillion possibilities.
With average hardware today, a cracker could break these types of passwords within a day using password dictionaries.
Word Correlation – Correct Horse Battery Staple Review
Following on from the above – with the problem of limited vocab, and the problem of user group behavior, you have scenarios where everybody is going to type in “Log me in please” instead of “avocado streetlight porch mercury.”
If the words are truly random, then the difficulty is much higher. But what if the words are tightly correlated? “Log me in please” would become the new “Password” or “123456.” You just can’t stop great minds from thinking alike!
Long Passwords Are Tough to Type
Also, let’s discuss user-friendliness, user error, and user fatigue. Do you know how many times I mistyped “Correct Horse Battery Staple” when writing this review? A bunch. Typing long words leads to errors, which are pretty annoying. The resulting confusion and frustration can reduce productivity, lock users out of systems, and lead to various kinds of chaos.
To Recap
The bottom line here is that phrase-style passwords are okay, but not great. For those few times that you need to memorize a password, create a unique sentence whose first letters result in something more than 16 characters. Otherwise, use a password manager to create and manage long passwords.
Permission to reprint xkcd comic is generously provided under https://xkcd.com/license.html Thanks, xkcd.
To receive more great cybersecurity content for business leaders, sign up for our monthly newsletter: https://fractionalciso.com/newsletter/



