
Building a cybersecurity program is a challenging and time-consuming project, especially if you have a workload full of engineering or IT responsibilities. Of course, it’s even more time-consuming if you don’t already have the cybersecurity knowledge needed to just start working on it. This is a project that many companies hire new, specialized full-time employees or professional services firms to lead and manage, after all!
You should, at least, take comfort in knowing that this project is very doable. Most strong technical employees can learn everything needed to implement a foundational cybersecurity program at small-to-midsize companies.
There are even a lot of free resources available to you, including this guide (and every other blog post by Fractional CISO).
This guide is intended to give you a short-term plan to get your cybersecurity program up and running. Links to other articles about different, relevant topics are included.
What is a Cybersecurity Program?
A cybersecurity program is a roadmap for a strong strategy when it comes to protecting private information and important assets at your organization.
Importance of Cybersecurity Programs
Cybersecurity programs protect your organization’s sensitive data, private customer information, and more against unauthorized access from hackers.
How to Build a Cybersecurity Program
They say the first step is always the hardest, but this is only partially true when it comes to cybersecurity programs.
Overcoming the organizational inertia to start a new initiative is hard, but the actual first tasks you’ll need to complete are surprisingly simple!
We’ve compiled a list of beginning steps for how to build a cybersecurity program below.
Step 1: Assemble a Cybersecurity Team
The first task to tackle is the assembly of a cybersecurity team that will manage the initiative.
“But wait!” I can hear you thinking, “my company doesn’t have any cybersecurity employees, that’s why they put me in charge of this!”
That’s okay, none of them have to be cybersecurity experts. Or even cybersecurity amateurs, really.
In our experience, new cybersecurity teams that are actually successful will have the three following roles. Note: none of the roles are meant to relate to a title of the employee you should use, they’re just the roles that the employee will play on the cybersecurity team.
1. Executive Sponsor
2. Program Manager
3. Technical Expert
Executive Sponsor
Cybersecurity programs require organizational change. Without buy-in from the highest levels of leadership, any new cybersecurity program is very likely to fail.
So the executive sponsor is a leader at the company who has the influence and commitment to drive the changes needed for success. It’s typically the founder, or someone with a “C” in their title like the CTO, CEO, or COO. Their job on the cybersecurity team can vary, depending on which specific title has this role.
The primary responsibilities are always to ensure the cybersecurity team has whatever resources they need and to ensure the entire organization buys in to the changes the cybersecurity program will bring. It’s important that this role is played by an executive leader because, if it’s someone at a lower level, they won’t have the authority needed to drive change. New changes being supported directly by the C-suite are more likely to be adopted by all employees than changes pushed by the Sales Manager, for example.
If it’s the Founder, CEO, or COO, their involvement likely starts and ends with this. If it’s the CTO, their job will likely be more involved, and may even be combined with the Technical Expert.
Program Manager
The program manager’s primary job is to organize the team and line up the resources it needs to succeed.
We have seen many different people with all sorts of different titles succeed in this role, including administrative assistants, office managers, documentation managers, project managers, program managers, and more!
The keys to success in this cybersecurity role are threefold:
- This person should be committed to the program and want to see it succeed.
- This person has the authority to organize the resources needed to enable the program’s success.
- This person is able to commit two-to-six working hours to cybersecurity each week.
Take note of what’s not listed – the program manager does not need to be a cybersecurity expert!
Technical Expert
Technical expertise is needed to implement many cybersecurity controls, even “entry-level” ones. That’s where the technical expert comes in!
Again, this person does not need to know much about cybersecurity. They do need to understand your organization’s network, software, cloud infrastructure, and any other system you want to secure.
While they don’t need to know a lot about cybersecurity to begin with, a legitimate interest and willingness to learn more about the subject will greatly improve their chances of success.
Common titles of individuals who hold this role are CTO and IT Director or Manager.
Step 2: Meet Weekly
Now that your cybersecurity team is assembled, it’s time to get to work! The first working task is to establish a weekly meeting cadence for the team.
Weekly meetings really help build momentum for a new cybersecurity initiative. The weekly meeting keeps the topic at the top of everybody’s mind and creates shorter deadlines for task completion than bi-weekly or monthly meetings would.
Once the cybersecurity program begins to mature, you can step the cadence down to bi-weekly or monthly. You’ll know you’ve hit this point when your weekly meetings start regularly sounding like this:
“Nothing to report!”
But what should the cybersecurity team actually talk about when getting started?
Step 3: Implement the Three Essential Cybersecurity Controls
The first project your fledgling cybersecurity team should undertake is the implementation of the Three Essential Cybersecurity Controls.
The three are: Multi-Factor Authentication (MFA), regular system patching, and cybersecurity awareness training.
Multi-Factor Authentication (MFA)
MFA is the use of a secondary authentication method, such as a one-time passcode, along with a regular password, to access an account or system.
While some attack methods are starting to bypass MFA, it remains the single most important technical control you can use in your organization. MFA prevents an attacker from being able to access key accounts with just a password. In order to access your accounts, an attacker would have to bypass or compromise the second authentication method too.
So what accounts should you use MFA on? All of them! Or at least, every account that permits the use of MFA.
Protecting every account is a huge task though, so start with the most high-value ones. These include your online office and email system (Google Workspace or Microsoft 365), bank accounts, cloud service providers (AWS), CRM systems, and more. Once the high-value accounts are protected, you can start to pursue other ones.
Regular System Patching
Make sure you regularly patch all of your systems, laptops, and applications.
As of 2019, approximately 60% of cybersecurity breaches were a result of unpatched systems. New vulnerabilities are found and patched every week. Unpatched systems make easy targets for attackers.
It’s a little like the “outrunning a bear” joke. You don’t have to be the most secure, so long as you’re more secure than the company next door!
Okay, that’s not a guarantee that you won’t be hacked, but many attackers prefer easy targets. Patching systems regularly makes you a much tougher target.
But wait, what does “regular” mean?
Easy … it depends! There’s no one-size-fits-all answer in cybersecurity. This likely depends on the technology stack that your organization uses. A good place to start is once-per-month. If you’re a Microsoft shop, you could plan to patch around “Patch Tuesday.”
Cybersecurity Awareness Training
One of the most common successful cyber attacks is phishing. While modern email providers do a pretty good job of filtering spam, some can still get through (especially if you’re on one of the basic Microsoft licenses).
The number one way to prevent phishing is to train your employees to not fall for phishing emails.
There are a ton of cybersecurity awareness training vendors out there and they all have their pros and cons. Evaluate some, and pick the one that will be the best fit for your business.
Once your training program is up and running, you should start running some phishing tests to check the results of your training, and to give your employees opportunities to actually put what they’ve learned into practice. It helps keep the training on their minds!

Leveling up your Cybersecurity Program
Congratulations! Now that you have a cybersecurity team, are meeting weekly, and have implemented some basic controls, you have a foundational cybersecurity program.
Your company is already significantly more secure than it used to be, but there’s still a lot more you can do to make improvements. The above plan is really foundational. It’s a universal starting point that you can build something greater on top of.
This is a good time to ask yourself: what are your goals for your cybersecurity program?
A few questions to consider:
- Do you have specific risks you need to protect yourself against?
- Do you want to meet a compliance standard, such as SOC 2 or ISO 27001?
- Is a new product or service launching soon?
- Are you hoping to have your company acquired?
- Is your business going through some sort of rapid growth or transformation?
Your organizational cybersecurity needs will become more unique very quickly once you start looking to uplevel your program, so it becomes tougher to provide such concrete guidance in the form of an article.
That said, there are a number of common practices that any mature cybersecurity program is going to have. Let’s take a look at what it takes to implement those.
Advanced Technical Controls in your Cybersecurity Program
MFA and patching are just the tip of the iceberg when it comes to technical cybersecurity controls. There are so many more available to you it can be hard to know where to start. We have a convenient list of nine controls in this article, which can be combined with the guidance found below.
The best place to start is to harden your cloud environments and software. Sadly, no cloud application or SaaS product comes out of the box in the “most secure” configuration or even a “relatively secure” configuration.
It’s worth digging into these platforms to make sure they are configured properly. This is especially important for Microsoft 365, Google Workspace, and AWS.
We have published hardening guides for Microsoft 365 and Google Workspace – click the prior links to go to them. Special note for Microsoft 365: We recommend upgrading to a higher license, or using a third-party email security tool to help protect against phishing emails. Google appears to perform much better at filtering phishing emails by default in comparison to Microsoft.
Other controls you should consider implementing at this stage include: Endpoint Detection & Response (EDR) tools, Mobile Device Management (MDM), encryption, network monitoring and logging, system backups, and more.
Key Cybersecurity Processes
Cybersecurity isn’t all about technical controls! There are a lot of business policies and administrative practices that go into keeping your organization safe. Let’s take a look at a few of the most important ones you might implement here.
One of the most important is access control. Even though former employees shouldn’t be allowed to access their emails or any accounts after their departure, far too many organizations don’t completely clean up their access! Therefore, you should create a robust employee offboarding process to ensure all of an employee’s access is properly cleaned up when they depart the organization.
Your organization doesn’t just face risks from internal configuration issues and vulnerabilities. Your vendors also expose you to a good deal of risk. This is why every mature cybersecurity program features a strong vendor management program – and why every cybersecurity compliance standard requires one! Implementing one will take a good deal of time and effort, but will substantially improve your cybersecurity maturity.

There’s also risk assessment and management itself. Once your cybersecurity program is up and running a risk assessment can be performed to help you understand what cybersecurity risks you still face. This assessment is used to refine your cybersecurity program by managing the unique risks you face. The best type of risk assessment is a quantitative risk assessment since it will help you prioritize the risks you treat.
Incident Response & Cyber Insurance
Incident Response is a particularly important cybersecurity process, and it’s never too early to create and practice your first incident response plan. It should be updated as your cybersecurity program matures to reflect new technology, policies, and resources you have in place.
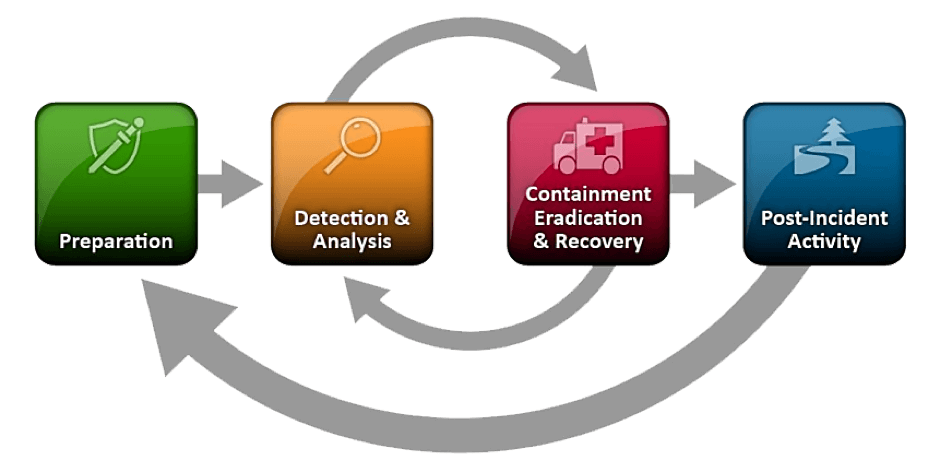
A good place to start with your plan is the NIST Incident Response Framework. It breaks the incident down into four stages: Preparation, Detection & Analysis, Containment, Eradication, & Recovery, and Post-Incident Activity.
It’s okay to start small. Any plan is better than no plan, and you will find ways to make improvements as you continue to practice it!
Related to incident response is cyber insurance. Does your company have it? Is the coverage sufficient? What resources does it require you to use during an incident?
Even if you do have cyber insurance, it likely isn’t risk-optimized to your company.
You should perform a cyber insurance review and update your coverage to match your company’s actual risk profile.
Ready to get Started?
If you’d like some help getting started with your cybersecurity program, let us know what you need through this form. We look forward to talking with you!
Want to get great cybersecurity content delivered to your inbox? Click here to sign up for our monthly newsletter, Tales from the Click.
To build a cybersecurity program, you need a team consisting of an executive sponsor, a project manager to line up resources, and a technical lead in implementing key cybersecurity defenses such as firewalls, antivirus, multi-factor authentication, employee training, monitoring systems, and more. These controls protect against cyber threats to keep data and systems safe.
Every organization should have a cybersecurity program, no matter its size or industry. Whether you’re a small business, a big corporation, a government agency, or a non-profit, you’re at risk of cyber-attacks if you use technology and handle sensitive information.
Start with a cybersecurity risk assessment first. This means discovering what threats are out there, how bad they could be, and how likely they are to happen. You should take steps such as checking your IT security, looking at past security problems, and considering industry rules.
Regular cybersecurity awareness training is crucial for employees to understand password security, phishing awareness, safe internet browsing, and social engineering tactics. They should be encouraged to report suspicious activity and breaches. Training should be interactive and engaging to ensure effective information retention.
Having an incident response plan is necessary for responding to cybersecurity incidents. The plan should include steps for contacting the appropriate parties, isolating affected systems, and notifying stakeholders. It should be regularly tested and updated, and incidents should be promptly investigated and documented for future prevention.
Regularly reviewing and updating your cybersecurity program is important to stay ahead of emerging threats, technological changes, and regulation updates. Conduct a thorough internal audit at least once a year or whenever significant changes occur in your IT infrastructure. Stay informed about cybersecurity trends and vulnerabilities and update your security measures.




